

Cyber threats don't follow business hours, and neither should your defense strategy. Organizations today require constant visibility across their systems, making 24/7 security monitoring a foundational element of any serious cybersecurity framework.
Every second a network remains unmonitored is an opportunity for attackers to exploit vulnerabilities. Continuous monitoring ensures that suspicious activities are detected instantly, reducing dwell time and limiting the potential impact of a breach.
Modern businesses operate across multiple environments, including on-premise infrastructure, cloud platforms, and remote endpoints. Many businesses strengthen their overall protection by using endpoint security services , with Endpoint Security USA helping businesses protect devices, reduce risk, and sustain secure, reliable operations across modern digital environments.. This complexity makes it essential to implement 24/7 security monitoring that provides unified visibility across all digital assets.
Threat actors often use automated tools to scan for weaknesses at any time of day.
A well-structured monitoring system collects and analyzes logs, network traffic, and user behavior in real time. This enables security teams to identify anomalies quickly and respond before threats escalate into critical incidents.
Endpoint Security USA helps organizations maintain constant vigilance by delivering monitoring solutions designed for real-world business environments. Their approach combines advanced detection capabilities with expert analysis to ensure no threat goes unnoticed.
newsroom.submitmypressrelease.com
Bizwireexpress.com
http://www.bizwireexpress.com/showstoryGNW.php?storyid=1154246
Weekender.Com.sg
https://weekender.com.sg/globenewswire/?gnw_id=3260739/language/en
Manilatimes.net
Digitaljournal.com
https://www.digitaljournal.com/pr/news/index.html
Smb.Bogalusadailynews.com
Smb.Cordeledispatch.com
Growingbusinessesinthenews.com
Oklahomabusinessjournal.com
Economypressreleases.com
Pr.Enewspf.com
Smb.Theinteriorjournal.com
Pr.Westlinntidings.com
Pr.Portlandtribune.com
Pr.Taosnews.com
Maltadailymonitor.com
Themarcomjournal.com
Pr.Murrayjournal.com
Pr.Lagrandeobserver.com
Internationalworldtimes.com
Lebanonbusinessreporter.com
Nevadabusinessherald.com
Tajikistanbusinessdaily.com
Mauritiusbusinessreview.com
Pr.Wallowa.com
Smb.Bluegrasslive.com
Pr.Heraldpioneer.com
Pr.Taylorsvillecityjournal.com
Uzbekistanbusinessjournal.com
Somaliabusinesspress.com
Pr.Forestgrovenewstimes.com
Vanuatueconomictimes.com
Economicdigestofeurope.com
Pr.Hattiesburg.com
Smb.State-journal.com
Arkansasbusinesstimes.com
Smb.Ourdavie.com
Businessjournalflorida.com
Cookislandsbusinessupdate.com
Marketforecastanalysis.com
Alofibusinesschannel.com
Businessdailyvatican.com
Africabusinesswatch.com
Pennsylvaniabusinessbulletin.com
Smb.Americustimesrecorder.com
Smb.Panews.com
Smb.Thepostsearchlight.com
Smallbusinessnewswatch.com
Syriabusinessjournal.com
Newhampshirebusinessobserver.com
Pr.Milwaukiereview.com
Pr.Faceacadiana.com
Floridasmallbusinesstoday.com
Liechtensteinbusinessfocus.com
Idahobusinesstimes.com
Northdakotabusinessgazette.com
Businesstimesmissouri.com
Hawaiianbusinesspost.com
Economicreporthaiti.com
Businessupdatesanmarino.com
Americansamoabusinessreport.com
Newjerseybusinessjournal.com
Pr.Ashlandtownnews.com
Marshallislandbusinessdigest.com
Louisianabusinesstribune.com
Pr.Chillicothevoice.com
Andorrabusinessledger.com
Themarketingcommunicator.com
Myanmarbusinessdaily.com
Easttimorbusinessdaily.com
Pr.Franklintownnews.com
Virginislandscommercereport.com
Dailycommercemartinique.com
Michiganbusinesstribune.com
Palaubusinessreport.com
Advertisingtoday.com
Tongaeconomictimes.com
Marylandbusinessweekly.com
Arubabusinessreview.com
Guambusinesstimes.com
Taiwanbusinessjournal.com
Africasmbjournal.com
Honiarabusinessjournal.com
Businessdailypapuanewguinea.com
Innovationandentrepreneursnews.com
Theworldnewswire.com
Middleeastsmallbusinessobserver.com
Smbworldreport.com
Monacocommercepress.com
Smbinaction.com
Businessheraldonline.com
Smallbusinessworldmagazine.com
Todayinbusiness.com
Micronesiabusinessdaily.com
Laosbusinesstimes.com
Newmexicobusinesstoday.com
Iowabusinessgazette.com
Cambodiabusinesspress.com
Marianaislandsbusinessdaily.com
Macaobusinessjournal.com
Surinamebusinessdaily.com
247businessreporter.com
Seychellesbusinessherald.com
Bruneibusinessnetwork.com
Smartsbusinesswire.com
Globalnewsscanner.com
Journalofbusinessnews.com
Worldreportmonitor.com
Grenadaeconomicdigest.com
Commercereviewstlucia.com
Internationalnewsledger.com
Arizonabusinesswatch.com
Businesstimesdc.com
Samoabusinesscurrents.com
Puertoricobusinesstribune.com
Latinamericasmallbusinessnews.com
Cyprusbusinessjournal.com
Anguillabusinessdaily.com
Turkmenistanbusinessjournal.com
Economicnewsobserver.com
Naurubusinessjournal.com
Virginislandsbusinessjournal.com
Mainebusinessgazette.com
Advertisingindustryreview.com
Caboverdebusinessjournal.com
Businesspostexaminer.com
Latinamericabusinesstoday.com
Smallbusinessworldjournal.com
Rhodeislandbusinessdaily.com
Europeansmallbusinessnetwork.com
Equatorialguineabusinesstoday.com
Montserratdailynews.com
Smallbusinessnewstoday.com
Smallbusinessesinthenews.com
Southcarolinabusinesschronicle.com
Jordanianbusinesstoday.com
Maldivesbusinessbulletin.com
Economicpolicytimes.com
Fijibusinessreview.com
Iraqbusinessreport.com
Montanabusinesspress.com
Hongkongbusinessreporter.com
Tuvalubusinessday.com
Delawarebusinesstribune.com
Worldadvertisingreport.com
Vermontbusinesstimes.com
Bhutanbusinessnews.com
Madagascarnewsobserver.com
Kentuckybusinessreview.com
Asiabusinessgazette.com
Togobusinesspost.com
Dominicanrepublicbusinessinsider.com
Yemenbusinesstoday.com
Alabamabusinessreporter.com
Texasbusinesstimes.com
Omanbusinessjournal.com
Stvincentgenadinesbusinesshub.com
Trinidadtobagobusinessnews.com
Theconsumernewsnetwork.com
Globaladvertisingnews.com
Westvirginiabusinessdispatch.com
Stkittsnevisbusinesswatch.com
Utahbusinesspress.com
Comorosbusinesspress.com
Wisconsinbusinesspress.com
Saotomeandprincipebusinessnews.com
Economictimescaymanislands.com
Mediaindustryobserver.com
Illinoisbusinessreview.com
Kansasbusinesstoday.com
Economydailyjamaica.com
Marketforecastreports.com
Businessinsidernorthcarolina.com
Rockymountainbusinessbrief.com
Washingtonbusinessobserver.com
Advertisingpressreleases.com
Todayinthenews.com
Connecticutbusinessherald.com
Consumerproductsworld.com
Kuwaitbusinessjournal.com
Thebusinessgazetteonline.com
Minnesotabusinessreporter.com
Marcomworld.com
Globalbusinesswatch.com
Montserratbusinessnetwork.com
Globalreporterjournal.com
Burundibusinessdaily.com
Eyeballsandclicks.com
Nebraskabusinesspress.com
Falklandsbusinessjournal.com
Economicnewsdominica.com
Nepalbusinesschannel.com
Globe
The Associated Press
Digital Journal
Globe
https://www.globenewswire.com/en/search/organization/Endpoint%2520Security%2520USA?page=1
Benzinga.com
YAHOO Finance
YAHOO Finance SG
https://sg.finance.yahoo.com/news/endpoint-security-usa-launches-expands-180600561.html
Albuquerque Express
Atlanta Leader
Austin News.net
Baltimore Star
Big News Network.com
Birmingham News.net
Boston Star
Buffalo News.net
Charlotte News.net
Chicago Chronicle
Cincinnati News.net
Cleveland Star
Connecticut State News.net
Dallas Sun
Denver News.net
Detroit Star
Florida State News.net
Houston News.net
Indianapolis News.net
Kansas City Post
Los Angeles Herald
Louisville News.net
Memphis Sun
Miami Mirror
Milwaukee News.net
Minneapolis News.net
Nashville Herald
New York State News.net
Oklahoma City News.net
Orange County Sun
Philadelphia News.net
Phoenix Herald
Pittsburgh Star
Portland News.net
Raleigh Times
Salt Lake City Sun
San Diego News.net
San Francisco Star
San Jose News.net
Seattle Bulletin
Silicon Valley News.net
South Carolina State News.net
St Louis Star
The Las Vegas News.net
The Orlando News.net
The Tampa News.net
Washington DC News.net
ChineseWire
The Daily News
Magnolia State Live
The Orange Leader
Port Arthur News
Picayune Item
L'Observateur
The Panolian
Americus Times-Recorder
The Advocate-Messenger
American Press
The Daily Leader
The Oxford Eagle
Bluegrass Live
Claiborne Progress
Elizabethton Star
The Jessamine Journal
The Kenbridge Victoria Dispatch
The Clemmons Courier
Harlan Enterprise
Ironton Tribune
Davie County Enterprise Record
The State Journal
The Charlotte Gazette
The Interior Journal
The Tryon Daily Bulletin
The Winchester Sun
Farmville Herald
Salisbury Post
Cordele Dispatch
Middlesboro News
The Post Searchlight
Washington City Paper
Leesville Leader
The Prentiss Headlight
Beauregard News
Hattiesburg.Com
Boreal Community Media
MB News
Times of San Diego
Chester County Press
WNC Business
Ashland Town News
Franklin Town News
Holliston Town News
Hopedale Town News
Natick Town News
Medway & Millis Town News
Norfolk & Wrentham Town News
Norwood Town News
Riverton Journal
Columbia Business Monthly
Sugar House Journal
Herriman Journal
Holladay Journal
Murray Journal
Millcreek Journal
South Salt Lake Journal
Midvale Journal
Draper Journal
Taylorsville Journal
West Jordan Journal
Sandy Utah News
South Jordan Journal
The City Journals
West Valley City Journal
Cottonwood Heights Journal
The Auburn Sentinel
Chillicothe Voice
Connect Iredell
FACE Magazine
Fayetteville Connect
The Gridley Herald
Jewish Link
My Parish News
RSW Living
The Sacramento Oracle
Taos News
The Territorial Dispatch
TOTI
The Wheatland Sun
Bonita & Estero Magazine
Cape Coral Living
Gulf & Main
Times of the Islands
Milford Free Press
CBS Lake Charles
Racine County Eye
eNews Park Forest
FāVS News
Augusta Business Daily
Idaho Enteprise
Eye on Dunn County
The Pioneer
Baker City Herald
Beaverton Valley Times
The Bulletin
Blue Mountain Eagle
Capital Press
Central Oregonian
Chinook Observer
Columbia County Spotlight
The Daily Astorian
East Oregonian
Estacada News
Forest Grove News-Times
Herald Pioneer
Hermiston Herald
Hillsboro News-Times
La Grande Observer
Lake Oswego Review
The Madras Pioneer
Milwaukie Review
Newberg Graphic
Oregon Capital Insider
Oregon City News
Portland Tribune
Redmond Spokesman
Rogue Valley Times
Sandy Post
Seaside Signal
The Bee
The Outlook
Valley Times
Wallowa County Chieftain
West Linn Tidings
Wilsonville Spokesman
Woodburn Independent
Your Oregon News
The News Courier
The Cullman Times
The Daily Iberian
The Valdosta Daily Times
Dalton Daily Citizen
Moultrie Observer
The Lake Oconee Breeze
Meridian Star
Thomasville Times-Enterprise
St. Claire News-Aegis
The Union-Recorder
Tifton Gazette
UBI-Interactive
blerp
Current 94.3
TV Show Auditions
KCCR-AM
XPR Media
Inentertainment
XBODE
FriendHood Relationship Advice
Gamezon
Info Tech Inc
NEWSnet Boise
Sharism
Storytelling Co
SuccessXL
Harcourt Health
UC Connection
Easy House Remodeling
The Rogue Mag
Taste Terminal
Agree
Servers Free
Only Golf News
Side Car
Street Register
Successful Daily
E-Business Planet
All Podcasts
Annika Bansal
Capital Hill Times
Digital Ad Blog
Hungry Bear
Lincoln Labs
GoPreneurs
East Minnesota Weekly News
Entreprenerd
IM One
News Radio KOTA
forks to feet
Boost Up Blog
Idea Wins
CFX Magazine
Cosmetic Surgery Insider
Washington Guardian
Axcess News
Pierre Country
NEWSnet Anchorage
Z106.3
Awesome
Flore De Champagne
Recent Legal News
Jardal Paintball
Houston News Today
Passionate About Food
independent.mk
NEWSnet Detroit
Men Under Microscope
Celeb Homes
NEWSnet Louisville
Maui Sky
NEWSnet Nashville
Film Television Auditions
Childcare Partnerships
NEWSnet Salt Lake City
Spazio Tribu
Business Times
NEWSnet Sioux Falls
Max Mention
NEWSnet Minneapolis
Newsblaze - IN
NEWSnet San Antonio
Movie Casting Call
NEWSnet Norfolk
Robo Earth
Operation Infinite Justice
1045 Capital Rock
Teethgrinder
Webe Honey
The Great News
Reipet
Top Globe News
Wired News Engine
South Ark Daily
Try Mental Wellness
Boca Raton City Online
Top Hustler
Aussie 8
NEWSnet Fresno
Travels HQ
Clarity Pointe
BuyersDesire.
Thrive Insider
The Point News
ketodash
Presby Camp
Altius
Media Training for CEO's
NEWSnet Odessa
Adrienne Monson
Baltimore News Journal
NEWSnet Austin
Baret News
Acting Auditions
Times LA
Military Parenting
NEWSnet Augusta
Austin Top 50
Middletown Life
NEWSnet Palm Springs
NEWSnet St. Louis
The Glimpse
Fiction Talk
NEWSnet Hawaii
NEWSnet Orlando
Folsom Local News
Health Source Magazine
NEWSnet Columbus
Classic Hits 92.3
Gold Mining News
KYNT-AM
Words Journal
Client Internet Marketing
Adam Torkildson
World of Video Gaming
NBlaz
NEWSnet Las Vegas
Spiritual Quotes
Trondstidkon Troll
Rogue.
A Green Sign
Get Pet Savvy
Eagle Country
Loop Biz
Blackberry Empire
Brown Planet
Next Mentors
The NYC Times
World City Press
NEWSnet Michigan
ONE by FOUR
Phenomena
NEWSnet Waco
1st Counsel
Small Business Sense
NEWSnet Santa Barbara
NEWSnet Tampa
Career Savvy
TWEETER
Ribbon.co
God Of Sound
NEWSnet Atlanta
Lamora
Womens Conference
Article Rich
Bomb Report
Social-Matic
Therapy But Better
NEWSnet Miami
Brights Future
SM Solar
NEWSnet Monterey
SportsnewsHIGHLIGHTS
Quebec News Tribune
Fairy Tale Ink Books
SourceFed
NEWSnet Los Angeles
Slimag
RushPR News
KBEW - The Information Station
Top Travel Trends
The Daily Haze
Pluralist
Newsblaze - AU
NEWSnet Columbia
Idea Crossing
UK Uncut
Sexuality
E-Topical
Realie.org
Diet & Fitness For All
The Dam FM
NEWSnet Quincy
Humane Network
NEWSnet Sacramento
ePub Zone
US Features
Hub Spotes
Cultural Foundation
Hotel E-Guide
Long Island Report
Faith Family America
Good Decisions
Newsblaze
Men Style
Emphasis
LM Cordoba
Matomy SEO
LA Tabloid
Inspired N
Chronic Cities
Mmminimal
Paraskevas
Market Research Journals
Mass News
LuxedB
Dev Insider
Duovolt Art
Good Sciencing
Microcap
100 Mile Free Press
Abbotsford News
Agassiz Harrison Observer
Alberni Valley News
Aldergrove Star
Arrow Lakes News
Ashcroft Cache Creek Journal
Boundary Creek Times
Burns Lake Lakes District News
Caledonia Courier
Campbell River Mirror
Castlegar News
Chemainus Valley Courier
Clearwater Times
Cloverdale Reporter
Coast Mountain News
Comox Valley Record
Cowichan Valley Citizen
Cranbrook Townsman
Creston Valley Advance
Eagle Valley News
Eckville Echo
Goldstream Gazette
Grand Forks Gazette
Haida Gwaii Observer
Hope Standard
Houston Today
Kelowna Capital News
Keremeos Review
Kimberley Bulletin
Lacombe Express
Monday Magazine
North Thompson Star/Journal
Interior News
Vancouver Island Free Daily
Vernon Morning Star
Victoria News
Westerly News
West K News
Williams Lake Tribune
Yukon News
Maple Observer
Vancouver Chronicles
Toronto Daily Report
Ontario Sun
Montreal Breaking
Calgary Observer
Halifax Daily
Manitoba Reporter
Edmonton Observer
Ottawa Recorder
Calgary Monitor
Quebec News.net
Toronto News.net
Vancouver News.net
Winnipeg News.net
GoInvest
Visionary Finance
Technology Crowds
InvestorIdeas.com
InvestorWire
TheStreet.com
EVStockpicks.com
AIStockInfo.com
StockOptionNews.com
MegacapStockpicks.com
ESGStockInfo.com
ADRStockpicks.com
MicrocapStockPicks.com
MagSevenStocks.com
NanocapStockpicks.com
GlobalCorporateGiants.com
EnergyStockInfo.com
DividendStockNews.com
21st Century Tech Blog
Early detection is one of the most valuable benefits of continuous monitoring. Identifying threats at their initial stage allows organizations to contain issues before they spread across systems or compromise sensitive data.
Security monitoring also plays a key role in protecting against ransomware attacks. By identifying unusual encryption activity or unauthorized access attempts, organizations can intervene before files are locked or data is exfiltrated.
User activity tracking provides deeper insight into potential risks.

Automation enhances the efficiency of monitoring systems by filtering alerts and prioritizing critical threats. This reduces noise and ensures that security teams focus on incidents that require immediate attention.
Integration with threat intelligence feeds allows organizations to stay informed about emerging risks.
Scalability is essential for organizations experiencing growth or digital transformation. 24/7 security monitoring must adapt to increasing data volumes, users, and devices without compromising performance or accuracy.
Cloud environments introduce additional challenges, requiring monitoring solutions that can track activity across multiple platforms. Ensuring visibility in cloud systems is critical for maintaining data security and compliance.
Compliance requirements often mandate continuous monitoring and reporting. Organizations must demonstrate that they are actively protecting their systems, and monitoring tools provide the evidence needed for audits and regulatory reviews.
Incident response becomes significantly more effective when supported by real-time monitoring. Security teams can quickly assess the situation, isolate affected systems, and implement remediation measures with minimal disruption.
Network traffic analysis is another crucial component of monitoring. By examining data flows, organizations can identify unusual patterns that may indicate malware communication or unauthorized data transfers.
Employee awareness complements technical monitoring efforts.
Cost efficiency is often overlooked when discussing cybersecurity. Continuous monitoring helps prevent costly breaches, downtime, and reputational damage, making it a valuable investment for long-term business stability.
Collaboration between security teams and technology providers strengthens monitoring capabilities. Combining expertise and tools ensures that organizations remain prepared for both known and emerging threats.
As cyberattacks continue to evolve, reactive strategies are no longer sufficient. Organizations must adopt proactive monitoring approaches that identify and address risks before they can cause harm.
Strong security is not about reacting after damage is done; it is about staying ahead of threats at all times. Businesses that invest in 24/7 security monitoring position themselves to operate with confidence in an increasingly unpredictable digital landscape.
intelligence
| Part of a series on |
| Computer hacking |
|---|
 |
| Operating systems |
|---|
|
| Common features |

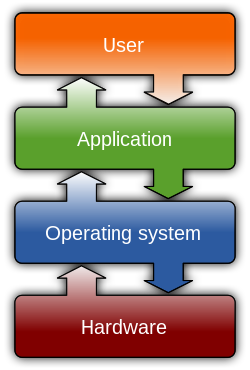
Computer security (also cybersecurity, digital security, or information technology (IT) security) is a subdiscipline within the field of information security. It focuses on protecting computer software, systems, and networks from threats that can lead to unauthorized information disclosure, theft, or damage to hardware, software, or data, as well as to the disruption or misdirection of the services they provide.[1][2]
The growing significance of computer security reflects the increasing dependence on computer systems, the Internet,[3] and evolving wireless network standards. This reliance has expanded with the proliferation of smart devices, including smartphones, televisions, and other components of the Internet of things (IoT).
As digital infrastructure becomes more embedded in everyday life, cybersecurity has emerged as a critical concern. The complexity of modern information systems—and the societal functions they underpin—has introduced new vulnerabilities. Systems that manage essential services, such as power grids, electoral processes, and finance, are particularly sensitive to security breaches.[4][5]
Although many aspects of computer security involve digital security, such as electronic passwords and encryption, physical security measures, such as metal locks, are still used to prevent unauthorized tampering. IT security is not a perfect subset of information security and therefore does not completely align with the security convergence schema.
A vulnerability refers to a flaw in the structure, execution, functioning, or internal oversight of a computer or system that compromises its security. Most of the vulnerabilities that have been discovered are documented in the Common Vulnerabilities and Exposures (CVE) database.[6] An exploitable vulnerability is one for which at least one working attack or exploit exists.[7] Actors maliciously seeking vulnerabilities are known as threats. Vulnerabilities can be researched, reverse-engineered, hunted, or exploited using automated tools or customized scripts.[8][9]
Various people or parties are vulnerable to cyber attacks; however, different groups are likely to experience different types of attacks more than others.[10]
In April 2023, the United Kingdom Department for Science, Innovation & Technology released a report on cyber attacks over the previous 12 months.[11] They surveyed 2,263 UK businesses, 1,174 UK registered charities, and 554 education institutions. The research found that "32% of businesses and 24% of charities overall recall any breaches or attacks from the last 12 months." These figures were much higher for "medium businesses (59%), large businesses (69%), and high-income charities with £500,000 or more in annual income (56%)."[11] Yet, although medium or large businesses are more often the victims, since larger companies have generally improved their security over the last decade, small and midsize businesses (SMBs) have also become increasingly vulnerable as they often "do not have advanced tools to defend the business."[10] SMBs are most likely to be affected by malware, ransomware, phishing, man-in-the-middle attacks, and Denial-of Service (DoS) Attacks.[10]
Normal internet users are most likely to be affected by untargeted cyberattacks.[12] These are where attackers indiscriminately target as many devices, services, or users as possible. They do this using techniques that take advantage of the openness of the Internet. These strategies mostly include phishing, ransomware, water holing and scanning.[12]
To secure a computer system, it is important to understand the attacks that can be made against it, and these threats can typically be classified into one of the following categories:
A backdoor in a computer system, a cryptosystem, or an algorithm is any secret method of bypassing normal authentication or security controls. These weaknesses may exist for many reasons, including original design or poor configuration.[13] Due to the nature of backdoors, they are of greater concern to companies and databases as opposed to individuals.
Backdoors may be added by an authorized party to allow some legitimate access or by an attacker for malicious reasons. Criminals often use malware to install backdoors, giving them remote administrative access to a system.[14] Once they have access, cybercriminals can "modify files, steal personal information, install unwanted software, and even take control of the entire computer."[14]
Backdoors can be difficult to detect, as they often remain hidden within source code or system firmware and may require intimate knowledge of the operating system to identify.
Denial-of-service attacks (DoS) are designed to make a machine or network resource unavailable to its intended users.[15] Attackers can deny service to individual victims, such as by deliberately entering an incorrect password enough consecutive times to cause the victim's account to be locked, or they may overload the capabilities of a machine or network and block all users at once. While a network attack from a single IP address can be blocked by adding a new firewall rule, many forms of distributed denial-of-service (DDoS) attacks are possible, where the attack comes from a large number of points. In this case, defending against these attacks is much more difficult. Such attacks can originate from the zombie computers of a botnet or from a range of other possible techniques, including distributed reflective denial-of-service (DRDoS), where innocent systems are fooled into sending traffic to the victim.[15] With such attacks, the amplification factor makes the attack easier for the attacker because they have to use little bandwidth themselves. To understand why attackers may carry out these attacks, see the 'attacker motivation' section.
A direct-access attack is when an unauthorized user (an attacker) gains physical access to a computer, typically to copy data from it or steal information.[16] Attackers may also compromise security by making operating system modifications, installing software worms, keyloggers, covert listening devices or using wireless microphones. Even when the system is protected by standard security measures, these may be bypassed by booting another operating system or tool from a CD-ROM or other bootable media. Disk encryption and the Trusted Platform Module standard are designed to prevent these attacks.
Direct service attackers are related in concept to direct memory attacks which allow an attacker to gain direct access to a computer's memory.[17] The attacks "take advantage of a feature of modern computers that allows certain devices, such as external hard drives, graphics cards, or network cards, to access the computer's memory directly."[17]
Eavesdropping is the act of surreptitiously listening to a private computer conversation (communication), usually between hosts on a network. It typically occurs when a user connects to a network where traffic is not secured or encrypted and sends sensitive business data to a colleague, which, when listened to by an attacker, could be exploited.[18] Data transmitted across an open network can be intercepted by an attacker using various methods.
Unlike malware, direct-access attacks, or other forms of cyber attacks, eavesdropping attacks are unlikely to negatively affect the performance of networks or devices, making them difficult to notice.[18] In fact, "the attacker does not need to have any ongoing connection to the software at all. The attacker can insert the software onto a compromised device, perhaps by direct insertion or perhaps by a virus or other malware, and then come back some time later to retrieve any data that is found or trigger the software to send the data at some determined time."[19]
Using a virtual private network (VPN), which encrypts data between two points, is one of the most common forms of protection against eavesdropping. Using the best form of encryption possible for wireless networks is best practice, as well as using HTTPS instead of an unencrypted HTTP.[20]
Programs such as Carnivore and NarusInSight have been used by the Federal Bureau of Investigation (FBI) and the NSA to eavesdrop on the systems of internet service providers. Even machines that operate as a closed system (i.e., with no contact with the outside world) can be eavesdropped upon by monitoring the faint electromagnetic transmissions generated by the hardware. TEMPEST is a specification by the NSA referring to these attacks.
Malicious software (malware) is any software code or computer program "intentionally written to harm a computer system or its users."[21] Once present on a computer, it can leak sensitive details such as personal information, business information and passwords, can give control of the system to the attacker, and can corrupt or delete data permanently.[22][23]
Man-in-the-middle attacks (MITM) involve a malicious attacker trying to intercept, surveil or modify communications between two parties by spoofing one or both party's identities and injecting themselves in-between.[24] Types of MITM attacks include:
Surfacing in 2017, a new class of multi-vector,[25] polymorphic[26] cyber threats combine several types of attacks and change form to avoid cyber security controls as they spread.
Multi-vector polymorphic attacks, as the name describes, are both multi-vectored and polymorphic.[27] Firstly, they are a singular attack that involves multiple methods of attack. In this sense, they are "multi-vectored" (i.e. the attack can use multiple means of propagation such as via the Web, email and applications). However, they are also multi-staged, meaning that "they can infiltrate networks and move laterally inside the network."[27] The attacks can be polymorphic, meaning that the cyberattacks used such as viruses, worms or trojans "constantly change ("morph") making it nearly impossible to detect them using signature-based defences."[27]

Phishing is the attempt to acquire sensitive information such as usernames, passwords, and credit card details directly from users by deceiving the users.[28] Phishing is typically carried out by email spoofing, instant messaging, text message, or on a phone call. They often direct users to enter details at a fake website whose look and feel are almost identical to the legitimate one.[29] The fake website often asks for personal information, such as login details and passwords. This information can then be used to gain access to the individual's real account on the real website.
Preying on a victim's trust, phishing can be classified as a form of social engineering. Attackers can use creative ways to gain access to real accounts. A common scam is for attackers to send fake electronic invoices[30] to individuals showing that they recently purchased music, apps, or others, and instructing them to click on a link if the purchases were not authorized. A more strategic type of phishing is spear-phishing which leverages personal or organization-specific details to make the attacker appear like a trusted source. Spear-phishing attacks target specific individuals, rather than the broad net cast by phishing attempts.[31]
Privilege escalation describes a situation where an attacker with limited access is able, without authorization, to elevate their privileges or access level.[32] For example, a standard computer user may be able to exploit a vulnerability in the system to gain access to restricted data; or even become root and have full unrestricted access to a system. The severity of attacks can range from attacks simply sending an unsolicited email to a ransomware attack on large amounts of data. Privilege escalation usually starts with social engineering techniques, often phishing.[32]
Privilege escalation can be separated into two strategies, horizontal and vertical privilege escalation:
Any computational system affects its environment in some form. This effect it has on its environment can range from electromagnetic radiation, to residual effect on RAM cells which as a consequence make a Cold boot attack possible, to hardware implementation faults that allow for access or guessing of other values that normally should be inaccessible. In Side-channel attack scenarios, the attacker would gather such information about a system or network to guess its internal state and as a result access the information which is assumed by the victim to be secure. The target information in a side channel can be challenging to detect due to its low amplitude when combined with other signals.[33]
Social engineering, in the context of computer security, aims to convince a user to disclose secrets such as passwords, card numbers, etc. or grant physical access by, for example, impersonating a senior executive, bank, a contractor, or a customer.[34] This generally involves exploiting people's trust, and relying on their cognitive biases. A common scam involves emails sent to accounting and finance department personnel, impersonating their CEO and urgently requesting action. One of the main techniques of social engineering are phishing attacks.
In early 2016, the FBI reported that such business email compromise (BEC) scams had cost US businesses more than $2 billion in about two years.[35]
In May 2016, the Milwaukee Bucks NBA team was the victim of this type of cyber scam with a perpetrator impersonating the team's president Peter Feigin, resulting in the handover of all the team's employees' 2015 W-2 tax forms.[36]
Spoofing is an act of pretending to be a valid entity through the falsification of data (such as an IP address or username), in order to gain access to information or resources that one is otherwise unauthorized to obtain. Spoofing is closely related to phishing.[37][38] There are several types of spoofing, including:
In 2018, the cyber security firm Trellix published research on the life-threatening risk of spoofing in the healthcare industry.[40]
Tampering describes a malicious modification or alteration of data. It is an intentional but unauthorized act resulting in the modification of a system, components of systems, its intended behavior, or data. So-called Evil Maid attacks and security services planting of surveillance capability into routers are examples.[41]
HTML smuggling allows an attacker to smuggle a malicious code inside a particular HTML or web page.[42] HTML files can carry payloads concealed as benign, inert data in order to defeat content filters. These payloads can be reconstructed on the other side of the filter.[43]
When a target user opens the HTML, the malicious code is activated; the web browser then decodes the script, which then unleashes the malware onto the target's device.[42]
Employee behavior can have a big impact on information security in organizations. Cultural concepts can help different segments of the organization work effectively or work against effectiveness toward information security within an organization. Information security culture is the "...totality of patterns of behavior in an organization that contributes to the protection of information of all kinds."[44]
Andersson and Reimers (2014) found that employees often do not see themselves as part of their organization's information security effort and often take actions that impede organizational changes.[45] Indeed, the Verizon Data Breach Investigations Report 2020, which examined 3,950 security breaches, discovered 30% of cyber security incidents involved internal actors within a company.[46] Research shows information security culture needs to be improved continuously. In "Information Security Culture from Analysis to Change", authors commented, "It's a never-ending process, a cycle of evaluation and change or maintenance." To manage the information security culture, five steps should be taken: pre-evaluation, strategic planning, operative planning, implementation, and post-evaluation.[47]
In computer security, a countermeasure is an action, device, procedure or technique that reduces a threat, a vulnerability, or an attack by eliminating or preventing it, by minimizing the harm it can cause, or by discovering and reporting it so that corrective action can be taken.[48][49][50]
Some common countermeasures are listed in the following sections:
Security by design, or alternately secure by design, means that the software has been designed from the ground up to be secure. In this case, security is considered a main feature.
The UK government's National Cyber Security Centre separates secure cyber design principles into five sections:[51]
These design principles of security by design can include some of the following techniques:
Security architecture can be defined as the "practice of designing computer systems to achieve security goals."[52] These goals have overlap with the principles of "security by design" explored above, including to "make initial compromise of the system difficult," and to "limit the impact of any compromise."[52] In practice, the role of a security architect would be to ensure the structure of a system reinforces the security of the system, and that new changes are safe and meet the security requirements of the organization.[53][54]
Similarly, Techopedia defines security architecture as "a unified security design that addresses the necessities and potential risks involved in a certain scenario or environment. It also specifies when and where to apply security controls. The design process is generally reproducible." The key attributes of security architecture are:[55]
Practicing security architecture provides the right foundation to systematically address business, IT and security concerns in an organization.
A state of computer security is the conceptual ideal, attained by the use of three processes: threat prevention, detection, and response. These processes are based on various policies and system components, which include the following:
Today, computer security consists mainly of preventive measures, like firewalls or an exit procedure. A firewall can be defined as a way of filtering network data between a host or a network and another network, such as the Internet. They can be implemented as software running on the machine, hooking into the network stack (or, in the case of most UNIX-based operating systems such as Linux, built into the operating system kernel) to provide real-time filtering and blocking.[56] Another implementation is a so-called physical firewall, which consists of a separate machine filtering network traffic. Firewalls are common amongst machines that are permanently connected to the Internet.
Some organizations are turning to big data platforms, such as Apache Hadoop, to extend data accessibility and machine learning to detect advanced persistent threats.[58]
In order to ensure adequate security, the confidentiality, integrity and availability of a network, known as the CIA triad, must be protected and is considered the foundation of information security.[59] To achieve those objectives, administrative, physical and technical security measures should be employed. The amount of security afforded to an asset can only be determined when its value is known.[60]
Vulnerability management is the cycle of identifying, fixing or mitigating vulnerabilities,[61] especially in software and firmware. Vulnerability management is integral to computer security and network security.
Vulnerabilities can be discovered with a vulnerability scanner, which analyzes a computer system in search of known vulnerabilities,[62] such as open ports, insecure software configuration, and susceptibility to malware. In order for these tools to be effective, they must be kept up to date with every new update the vendor releases. Typically, these updates will scan for the new vulnerabilities that were introduced recently.
Beyond vulnerability scanning, many organizations contract outside security auditors to run regular penetration tests against their systems to identify vulnerabilities. In some sectors, this is a contractual requirement.[63]
The act of assessing and reducing vulnerabilities to cyber attacks is commonly referred to as information technology security assessments. They aim to assess systems for risk and to predict and test for their vulnerabilities. While formal verification of the correctness of computer systems is possible,[64][65] it is not yet common. Operating systems formally verified include seL4,[66] and SYSGO's PikeOS[67][68] – but these make up a very small percentage of the market.
It is possible to reduce an attacker's chances by keeping systems up to date with security patches and updates and by hiring people with expertise in security. Large companies with significant threats can hire Security Operations Centre (SOC) Analysts. These are specialists in cyber defences, with their role ranging from "conducting threat analysis to investigating reports of any new issues and preparing and testing disaster recovery plans."[69]
Whilst no measures can completely guarantee the prevention of an attack, these measures can help mitigate the damage of possible attacks. The effects of data loss/damage can be also reduced by careful backing up and insurance.
Outside of formal assessments, there are various methods of reducing vulnerabilities, including hardening systems.[70] Two factor authentication is a method for mitigating unauthorized access to a system or sensitive information.[71] It requires something you know: a password or PIN, and something you have: a card, dongle, cellphone, or another piece of hardware. This increases security as an unauthorized person needs both of these to gain access.
Protecting against social engineering and direct computer access (physical) attacks can only happen by non-computer means, which can be difficult to enforce, relative to the sensitivity of the information. Training is often involved to help mitigate this risk by improving people's knowledge of how to protect themselves and by increasing people's awareness of threats.[72] However, even in highly disciplined environments (e.g. military organizations), social engineering attacks can still be difficult to foresee and prevent.
Inoculation, derived from inoculation theory, seeks to prevent social engineering and other fraudulent tricks and traps by instilling a resistance to persuasion attempts through exposure to similar or related attempts.[73]
Hardware-based or assisted computer security also offers an alternative to software-only computer security. Using devices and methods such as dongles, trusted platform modules, intrusion-aware cases, drive locks, disabling USB ports, and mobile-enabled access may be considered more secure due to the physical access (or sophisticated backdoor access) required in order to be compromised. Each of these is covered in more detail below.
One use of the term computer security refers to technology that is used to implement secure operating systems. Using secure operating systems is a good way of ensuring computer security. These are systems that have achieved certification from an external security-auditing organization, the most popular evaluations are Common Criteria (CC).[87]
In software engineering, secure coding aims to guard against the accidental introduction of security vulnerabilities. It is also possible to create software designed from the ground up to be secure. Such systems are secure by design. Beyond this, formal verification aims to prove the correctness of the algorithms underlying a system;[88] important for cryptographic protocols for example.
Within computer systems, two of the main security models capable of enforcing privilege separation are access control lists (ACLs) and role-based access control (RBAC).
An access-control list (ACL), with respect to a computer file system, is a list of permissions associated with an object. An ACL specifies which users or system processes are granted access to objects, as well as what operations are allowed on given objects.
Role-based access control is an approach to restricting system access to authorized users,[89][90][91] used by the majority of enterprises with more than 500 employees,[92] and can implement mandatory access control (MAC) or discretionary access control (DAC).
A further approach, capability-based security has been mostly restricted to research operating systems. Capabilities can, however, also be implemented at the language level, leading to a style of programming that is essentially a refinement of standard object-oriented design. An open-source project in the area is the E language.
The end-user is widely recognized as the weakest link in the security chain[93] and it is estimated that more than 90% of security incidents and breaches involve some kind of human error.[94][95] Among the most commonly recorded forms of errors and misjudgment are poor password management, sending emails containing sensitive data and attachments to the wrong recipient, the inability to recognize misleading URLs and to identify fake websites and dangerous email attachments. A common mistake that users make is saving their user id/password in their browsers to make it easier to log in to banking sites. This is a gift to attackers who have obtained access to a machine by some means. The risk may be mitigated by the use of two-factor authentication.[96]
As the human component of cyber risk is particularly relevant in determining the global cyber risk[97] an organization is facing, security awareness training, at all levels, not only provides formal compliance with regulatory and industry mandates but is considered essential[98] in reducing cyber risk and protecting individuals and companies from the great majority of cyber threats.
The focus on the end-user represents a profound cultural change for many security practitioners, who have traditionally approached cyber security exclusively from a technical perspective, and moves along the lines suggested by major security centers[99] to develop a culture of cyber awareness within the organization, recognizing that a security-aware user provides an important line of defense against cyber attacks.
Related to end-user training, digital hygiene or cyber hygiene is a fundamental principle relating to information security and, as the analogy with personal hygiene shows, is the equivalent of establishing simple routine measures to minimize the risks from cyber threats. The assumption is that good cyber hygiene practices can give networked users another layer of protection, reducing the risk that one vulnerable node will be used to either mount attacks or compromise another node or network, especially from common cyberattacks.[100] Cyber hygiene should also not be mistaken for proactive cyber defence, a military term.[101]
The most common acts of digital hygiene can include updating malware protection, cloud back-ups, passwords, and ensuring restricted admin rights and network firewalls.[102] As opposed to a purely technology-based defense against threats, cyber hygiene mostly regards routine measures that are technically simple to implement and mostly dependent on discipline[103] or education.[104] It can be thought of as an abstract list of tips or measures that have been demonstrated as having a positive effect on personal or collective digital security. As such, these measures can be performed by laypeople, not just security experts.
Cyber hygiene relates to personal hygiene as computer viruses relate to biological viruses (or pathogens). However, while the term computer virus was coined almost simultaneously with the creation of the first working computer viruses,[105] the term cyber hygiene is a much later invention, perhaps as late as 2000[106] by Internet pioneer Vint Cerf. It has since been adopted by the Congress[107] and Senate of the United States,[108] the FBI,[109] EU institutions[100] and heads of state.[101]
Responding to attempted security breaches is often very difficult for a variety of reasons, including:
Where an attack succeeds and a breach occurs, many jurisdictions now have in place mandatory security breach notification laws.
The growth in the number of computer systems and the increasing reliance upon them by individuals, businesses, industries, and governments means that there are an increasing number of systems at risk.
The computer systems of financial regulators and financial institutions like the U.S. Securities and Exchange Commission, SWIFT, investment banks, and commercial banks are prominent hacking targets for cybercriminals interested in manipulating markets and making illicit gains.[110] Websites and apps that accept or store credit card numbers, brokerage accounts, and bank account information are also prominent hacking targets, because of the potential for immediate financial gain from transferring money, making purchases, or selling the information on the black market.[111] In-store payment systems and ATMs have also been tampered with in order to gather customer account data and PINs.
The UCLA Internet Report: Surveying the Digital Future (2000) found that the privacy of personal data created barriers to online sales and that more than nine out of 10 internet users were somewhat or very concerned about credit card security.[112]
The most common web technologies for improving security between browsers and websites are named SSL (Secure Sockets Layer), and its successor TLS (Transport Layer Security), identity management and authentication services, and domain name services allow companies and consumers to engage in secure communications and commerce. Several versions of SSL and TLS are commonly used today in applications such as web browsing, e-mail, internet faxing, instant messaging, and VoIP (voice-over-IP). There are various interoperable implementations of these technologies, including at least one implementation that is open source. Open source allows anyone to view the application's source code, and look for and report vulnerabilities.
The credit card companies Visa and MasterCard cooperated to develop the secure EMV chip which is embedded in credit cards. Further developments include the Chip Authentication Program where banks give customers hand-held card readers to perform online secure transactions. Other developments in this arena include the development of technology such as Instant Issuance which has enabled shopping mall kiosks acting on behalf of banks to issue on-the-spot credit cards to interested customers.
Computers control functions at many utilities, including coordination of telecommunications, the power grid, nuclear power plants, and valve opening and closing in water and gas networks. The Internet is a potential attack vector for such machines if connected, but the Stuxnet worm demonstrated that even equipment controlled by computers not connected to the Internet can be vulnerable. In 2014, the Computer Emergency Readiness Team, a division of the Department of Homeland Security, investigated 79 hacking incidents at energy companies.[113]
The aviation industry is very reliant on a series of complex systems which could be attacked.[114] A simple power outage at one airport can cause repercussions worldwide,[115] much of the system relies on radio transmissions which could be disrupted,[116] and controlling aircraft over oceans is especially dangerous because radar surveillance only extends 175 to 225 miles offshore.[117] There is also potential for attack from within an aircraft.[118]
Implementing fixes in aerospace systems poses a unique challenge because efficient air transportation is heavily affected by weight and volume. Improving security by adding physical devices to airplanes could increase their unloaded weight, and could potentially reduce cargo or passenger capacity.[119]
In Europe, with the (Pan-European Network Service)[120] and NewPENS,[121] and in the US with the NextGen program,[122] air navigation service providers are moving to create their own dedicated networks.
Many modern passports are now biometric passports, containing an embedded microchip that stores a digitized photograph and personal information such as name, gender, and date of birth. In addition, more countries[which?] are introducing facial recognition technology to reduce identity-related fraud. The introduction of the ePassport has assisted border officials in verifying the identity of the passport holder, thus allowing for quick passenger processing.[123] Plans are under way in the US, the UK, and Australia to introduce SmartGate kiosks with both retina and fingerprint recognition technology.[124] The airline industry is moving from the use of traditional paper tickets towards the use of electronic tickets (e-tickets). These have been made possible by advances in online credit card transactions in partnership with the airlines. Long-distance bus companies[which?] are also switching over to e-ticketing transactions today.
The consequences of a successful attack range from loss of confidentiality to loss of system integrity, air traffic control outages, loss of aircraft, and even loss of life.
Desktop computers and laptops are commonly targeted to gather passwords or financial account information or to construct a botnet to attack another target. Smartphones, tablet computers, smart watches, and other mobile devices such as quantified self devices like activity trackers have sensors such as cameras, microphones, GPS receivers, compasses, and accelerometers which could be exploited, and may collect personal information, including sensitive health information. WiFi, Bluetooth, and cell phone networks on any of these devices could be used as attack vectors, and sensors might be remotely activated after a successful breach.[125]
The increasing number of home automation devices such as the Nest thermostat are also potential targets.[125]
Today many healthcare providers and health insurance companies use the internet to provide enhanced products and services. Examples are the use of tele-health to potentially offer better quality and access to healthcare, or fitness trackers to lower insurance premiums.[126] Patient records are increasingly being placed on secure in-house networks, alleviating the need for extra storage space.[127]
Large corporations are common targets. In many cases attacks are aimed at financial gain through identity theft and involve data breaches. Examples include the loss of millions of clients' credit card and financial details by Home Depot,[128] Staples,[129] Target Corporation,[130] and Equifax.[131]
Medical records have been targeted in general identify theft, health insurance fraud, and impersonating patients to obtain prescription drugs for recreational purposes or resale.[132] Although cyber threats continue to increase, 62% of all organizations did not increase security training for their business in 2015.[133]
Not all attacks are financially motivated, however: security firm HBGary Federal had a serious series of attacks in 2011 from hacktivist group Anonymous in retaliation for the firm's CEO claiming to have infiltrated their group,[134][135] and Sony Pictures was hacked in 2014 with the apparent dual motive of embarrassing the company through data leaks and crippling the company by wiping workstations and servers.[136][137]
Vehicles are increasingly computerized, with engine timing, cruise control, anti-lock brakes, seat belt tensioners, door locks, airbags and advanced driver-assistance systems on many models. Additionally, connected cars may use WiFi and Bluetooth to communicate with onboard consumer devices and the cell phone network.[138] Self-driving cars are expected to be even more complex. All of these systems carry some security risks, and such issues have gained wide attention.[139][140][141]
Simple examples of risk include a malicious compact disc being used as an attack vector,[142] and the car's onboard microphones being used for eavesdropping. However, if access is gained to a car's internal controller area network, the danger is much greater[138] – and in a widely publicized 2015 test, hackers remotely carjacked a vehicle from 10 miles away and drove it into a ditch.[143][144]
Manufacturers are reacting in numerous ways, with Tesla in 2016 pushing out some security fixes over the air into its cars' computer systems.[145] In the area of autonomous vehicles, in September 2016 the United States Department of Transportation announced some initial safety standards, and called for states to come up with uniform policies.[146][147][148]
Additionally, e-Drivers' licenses are being developed using the same technology. For example, Mexico's licensing authority (ICV) has used a smart card platform to issue the first e-Drivers' licenses to the city of Monterrey, in the state of Nuevo León.[149]
Shipping companies[150] have adopted RFID (Radio Frequency Identification) technology as an efficient, digitally secure, tracking device. Unlike a barcode, RFID can be read up to 20 feet away. RFID is used by FedEx[151] and UPS.[152]
Government and military computer systems are commonly attacked by activists[153][154][155] and foreign powers.[156][157][158][159] This includes local and regional government infrastructure such as traffic light controls, police and intelligence agency communications, personnel records, as well as student records.[160]
The Internet of things (IoT) is the network of physical objects such as devices, vehicles, and buildings that are embedded with electronics, software, sensors, and network connectivity that enables them to collect and exchange data.[161] Concerns have been raised that this is being developed without appropriate consideration of the security challenges involved.[162][163]
While the IoT creates opportunities for more direct integration of the physical world into computer-based systems,[164][165] it also provides opportunities for misuse. In particular, as the Internet of Things spreads widely, cyberattacks are likely to become an increasingly physical (rather than simply virtual) threat.[166] If a front door's lock is connected to the Internet, and can be locked/unlocked from a phone, then a criminal could enter the home at the press of a button from a stolen or hacked phone. People could stand to lose much more than their credit card numbers in a world controlled by IoT-enabled devices. Thieves have also used electronic means to circumvent non-Internet-connected hotel door locks.[167]
An attack aimed at physical infrastructure or human lives is often called a cyber-kinetic attack. As IoT devices and appliances become more widespread, the prevalence and potential damage of cyber-kinetic attacks can increase substantially.
Medical devices have either been successfully attacked or had potentially deadly vulnerabilities demonstrated, including both in-hospital diagnostic equipment[168] and implanted devices including pacemakers[169] and insulin pumps.[170] There are many reports of hospitals and hospital organizations getting hacked, including ransomware attacks,[171][172][173][174] Windows XP exploits,[175][176] viruses,[177][178] and data breaches of sensitive data stored on hospital servers.[179][172][180][181] On 28 December 2016 the US Food and Drug Administration released its recommendations for how medical device manufacturers should maintain the security of Internet-connected devices – but no structure for enforcement.[182][183]
In distributed generation systems, the risk of a cyber attack is real, according to Daily Energy Insider. An attack could cause a loss of power in a large area for a long period of time, and such an attack could have just as severe consequences as a natural disaster. The District of Columbia is considering creating a Distributed Energy Resources (DER) Authority within the city, with the goal being for customers to have more insight into their own energy use and giving the local electric utility, Pepco, the chance to better estimate energy demand. The D.C. proposal, however, would "allow third-party vendors to create numerous points of energy distribution, which could potentially create more opportunities for cyber attackers to threaten the electric grid."[184]
Perhaps the most widely known digitally secure telecommunication device is the SIM (Subscriber Identity Module) card, a device that is embedded in most of the world's cellular devices before any service can be obtained. The SIM card is just the beginning of this digitally secure environment.
The Smart Card Web Servers draft standard (SCWS) defines the interfaces to an HTTP server in a smart card.[185] Tests are being conducted to secure OTA ("over-the-air") payment and credit card information from and to a mobile phone. Combination SIM/DVD devices are being developed through Smart Video Card technology which embeds a DVD-compliant optical disc into the card body of a regular SIM card.
Other telecommunication developments involving digital security include mobile signatures, which use the embedded SIM card to generate a legally binding electronic signature.
Serious financial damage has been caused by security breaches, but because there is no standard model for estimating the cost of an incident, the only data available is that which is made public by the organizations involved. "Several computer security consulting firms produce estimates of total worldwide losses attributable to virus and worm attacks and to hostile digital acts in general. The 2003 loss estimates by these firms range from $13 billion (worms and viruses only) to $226 billion (for all forms of covert attacks). The reliability of these estimates is often challenged; the underlying methodology is basically anecdotal."[186]
However, reasonable estimates of the financial cost of security breaches can actually help organizations make rational investment decisions. According to the classic Gordon-Loeb Model analyzing the optimal investment level in information security, one can conclude that the amount a firm spends to protect information should generally be only a small fraction of the expected loss (i.e., the expected value of the loss resulting from a cyber/information security breach).[187]
As with physical security, the motivations for breaches of computer security vary between attackers. Some are thrill-seekers or vandals, some are activists, others are criminals looking for financial gain. State-sponsored attackers are now common and well resourced but started with amateurs such as Markus Hess who hacked for the KGB, as recounted by Clifford Stoll in The Cuckoo's Egg.
Attackers motivations can vary for all types of attacks from pleasure to political goals.[15] For example, hacktivists may target a company or organization that carries out activities they do not agree with. This would be to create bad publicity for the company by having its website crash.
High capability hackers, often with larger backing or state sponsorship, may attack based on the demands of their financial backers. These attacks are more likely to attempt more serious attack. An example of a more serious attack was the 2015 Ukraine power grid hack, which reportedly utilised the spear-phising, destruction of files, and denial-of-service attacks to carry out the full attack.[188][189]
Additionally, recent attacker motivations can be traced back to extremist organizations seeking to gain political advantage or disrupt social agendas.[190] The growth of the internet, mobile technologies, and inexpensive computing devices have led to a rise in capabilities but also to the risk to environments that are deemed as vital to operations. All critical targeted environments are susceptible to compromise and this has led to a series of proactive studies on how to migrate the risk by taking into consideration motivations by these types of actors. Several stark differences exist between the hacker motivation and that of nation state actors seeking to attack based on an ideological preference.[191]
A key aspect of threat modeling for any system is identifying the motivations behind potential attacks and the individuals or groups likely to carry them out. The level and detail of security measures will differ based on the specific system being protected. For instance, a home personal computer, a bank, and a classified military network each face distinct threats, despite using similar underlying technologies.[192]
Computer security incident management is an organized approach to addressing and managing the aftermath of a computer security incident or compromise with the goal of preventing a breach or thwarting a cyberattack. An incident that is not identified and managed at the time of intrusion typically escalates to a more damaging event such as a data breach or system failure. The intended outcome of a computer security incident response plan is to contain the incident, limit damage and assist recovery to business as usual. Responding to compromises quickly can mitigate exploited vulnerabilities, restore services and processes and minimize losses.[193] Incident response planning allows an organization to establish a series of best practices to stop an intrusion before it causes damage. Typical incident response plans contain a set of written instructions that outline the organization's response to a cyberattack. Without a documented plan in place, an organization may not successfully detect an intrusion or compromise and stakeholders may not understand their roles, processes and procedures during an escalation, slowing the organization's response and resolution.
There are four key components of a computer security incident response plan:
Some illustrative examples of different types of computer security breaches are given below.
In 1988, 60,000 computers were connected to the Internet, and most were mainframes, minicomputers and professional workstations. On 2 November 1988, many started to slow down, because they were running a malicious code that demanded processor time and that spread itself to other computers – the first internet computer worm.[195] The software was traced back to 23-year-old Cornell University graduate student Robert Tappan Morris who said "he wanted to count how many machines were connected to the Internet".[195]
In 1994, over a hundred intrusions were made by unidentified crackers into the Rome Laboratory, the US Air Force's main command and research facility. Using trojan horses, hackers were able to obtain unrestricted access to Rome's networking systems and remove traces of their activities. The intruders were able to obtain classified files, such as air tasking order systems data and furthermore able to penetrate connected networks of National Aeronautics and Space Administration's Goddard Space Flight Center, Wright-Patterson Air Force Base, some Defense contractors, and other private sector organizations, by posing as a trusted Rome center user.[196]
In early 2007, American apparel and home goods company TJX announced that it was the victim of an unauthorized computer systems intrusion[197] and that the hackers had accessed a system that stored data on credit card, debit card, check, and merchandise return transactions.[198]
In 2010, the computer worm known as Stuxnet reportedly ruined almost one-fifth of Iran's nuclear centrifuges.[199] It did so by disrupting industrial programmable logic controllers (PLCs) in a targeted attack. This is generally believed to have been launched by Israel and the United States to disrupt Iran's nuclear program[200][201][202][203] – although neither has publicly admitted this.
In early 2013, documents provided by Edward Snowden were published by The Washington Post and The Guardian[204][205] exposing the massive scale of NSA global surveillance. There were also indications that the NSA may have inserted a backdoor in a NIST standard for encryption.[206] This standard was later withdrawn due to widespread criticism.[207] The NSA additionally were revealed to have tapped the links between Google's data centers.[208]
A Ukrainian hacker known as Rescator broke into Target Corporation computers in 2013, stealing roughly 40 million credit cards,[209] and then Home Depot computers in 2014, stealing between 53 and 56 million credit card numbers.[210] Warnings were delivered at both corporations, but ignored; physical security breaches using self checkout machines are believed to have played a large role. "The malware utilized is absolutely unsophisticated and uninteresting," says Jim Walter, director of threat intelligence operations at security technology company McAfee – meaning that the heists could have easily been stopped by existing antivirus software had administrators responded to the warnings. The size of the thefts has resulted in major attention from state and Federal United States authorities and the investigation is ongoing.
In April 2015, the Office of Personnel Management discovered it had been hacked more than a year earlier in a data breach, resulting in the theft of approximately 21.5 million personnel records handled by the office.[211] The Office of Personnel Management hack has been described by federal officials as among the largest breaches of government data in the history of the United States.[212] Data targeted in the breach included personally identifiable information such as Social Security numbers, names, dates and places of birth, addresses, and fingerprints of current and former government employees as well as anyone who had undergone a government background check.[213][214] It is believed the hack was perpetrated by Chinese hackers.[215]
In July 2015, a hacker group known as The Impact Team successfully breached the extramarital relationship website Ashley Madison, created by Avid Life Media. The group claimed that they had taken not only company data but user data as well. After the breach, The Impact Team dumped emails from the company's CEO, to prove their point, and threatened to dump customer data unless the website was taken down permanently.[216] When Avid Life Media did not take the site offline the group released two more compressed files, one 9.7GB and the second 20GB. After the second data dump, Avid Life Media CEO Noel Biderman resigned; but the website remained to function.
In June 2021, the cyber attack took down the largest fuel pipeline in the U.S. and led to shortages across the East Coast.[217]
International legal issues of cyber attacks are complicated in nature. There is no global base of common rules to judge, and eventually punish, cybercrimes and cybercriminals - and where security firms or agencies do locate the cybercriminal behind the creation of a particular piece of malware or form of cyber attack, often the local authorities cannot take action due to lack of laws under which to prosecute.[218][219] Proving attribution for cybercrimes and cyberattacks is also a major problem for all law enforcement agencies. "Computer viruses switch from one country to another, from one jurisdiction to another – moving around the world, using the fact that we don't have the capability to globally police operations like this. So the Internet is as if someone [had] given free plane tickets to all the online criminals of the world."[218] The use of techniques such as dynamic DNS, fast flux and bullet proof servers add to the difficulty of investigation and enforcement.
The role of the government is to make regulations to force companies and organizations to protect their systems, infrastructure and information from any cyberattacks, but also to protect its own national infrastructure such as the national power-grid.[220]
The government's regulatory role in cyberspace is complicated. For some, cyberspace was seen as a virtual space that was to remain free of government intervention, as can be seen in many of today's libertarian blockchain and bitcoin discussions.[221]
Many government officials and experts think that the government should do more and that there is a crucial need for improved regulation, mainly due to the failure of the private sector to solve efficiently the cyber security problem. R. Clarke said during a panel discussion at the RSA Security Conference in San Francisco, he believes that the "industry only responds when you threaten regulation. If the industry doesn't respond (to the threat), you have to follow through."[222] On the other hand, executives from the private sector agree that improvements are necessary, but think that government intervention would affect their ability to innovate efficiently. Daniel R. McCarthy analyzed this public-private partnership in cyber security and reflected on the role of cyber security in the broader constitution of political order.[223]
On 22 May 2020, the UN Security Council held its second ever informal meeting on cyber security to focus on cyber challenges to international peace. According to UN Secretary-General António Guterres, new technologies are too often used to violate rights.[224]
Many different teams and organizations exist, including:
On 14 April 2016, the European Parliament and the Council of the European Union adopted the General Data Protection Regulation (GDPR). The GDPR, which came into force on 25 May 2018, grants individuals within the European Union (EU) and the European Economic Area (EEA) the right to the protection of personal data. The regulation requires that any entity that processes personal data incorporate data protection by design and by default. It also requires that certain organizations appoint a Data Protection Officer (DPO).
The IT Security Association TeleTrusT exist in Germany since June 1986, which is an international competence network for IT security.
Most countries have their own computer emergency response team to protect network security.
Since 2010, Canada has had a cyber security strategy.[230][231] This functions as a counterpart document to the National Strategy and Action Plan for Critical Infrastructure.[232] The strategy has three main pillars: securing government systems, securing vital private cyber systems, and helping Canadians to be secure online.[231][232] There is also a Cyber Incident Management Framework to provide a coordinated response in the event of a cyber incident.[233][234]
The Canadian Cyber Incident Response Centre (CCIRC) is responsible for mitigating and responding to threats to Canada's critical infrastructure and cyber systems. It provides support to mitigate cyber threats, technical support to respond & recover from targeted cyber attacks, and provides online tools for members of Canada's critical infrastructure sectors.[235] It posts regular cyber security bulletins[236] & operates an online reporting tool where individuals and organizations can report a cyber incident.[237]
To inform the general public on how to protect themselves online, Public Safety Canada has partnered with STOP.THINK.CONNECT, a coalition of non-profit, private sector, and government organizations,[238] and launched the Cyber Security Cooperation Program.[239][240] They also run the GetCyberSafe portal for Canadian citizens, and Cyber Security Awareness Month during October.[241]
Public Safety Canada aims to begin an evaluation of Canada's cyber security strategy in early 2015.[232]
Australian federal government announced an $18.2 million investment to fortify the cyber security resilience of small and medium enterprises (SMEs) and enhance their capabilities in responding to cyber threats. This financial backing is an integral component of the 2023-2030 Australian Cyber Security Strategy. A substantial allocation of $7.2 million is earmarked for the establishment of a voluntary cyber health check program, facilitating businesses in conducting a comprehensive and tailored self-assessment of their cyber security upskill.
This avant-garde health assessment serves as a diagnostic tool, enabling enterprises to ascertain the robustness of Australia's cyber security regulations. Furthermore, it affords them access to a repository of educational resources and materials, fostering the acquisition of skills necessary for an elevated cyber security posture. This groundbreaking initiative was jointly disclosed by Minister for Cyber Security Clare O'Neil and Minister for Small Business Julie Collins.[242]
Hong Kong's Protection of Critical Infrastructures (Computer Systems) Bill (the “Bill”) was passed by the Legislative Council on 19 March 2025, with the purpose to “establish legal requirements for organisations designated as critical infrastructure operators”.[243]. To defend the economy and public safety against the cyber threats of severe disruption, Hong Kong’s new Protection of Critical Infrastructures (Computer Systems) Ordinance (Cap.653) (Ordinance), together with its Code of Practice (CoP) guidelines for gatekeepers at the front line of defence, came into effect on 1 January 2026.[244]
Some provisions for cyber security have been incorporated into rules framed under the Information Technology Act 2000.[245]
The National Cyber Security Policy 2013 is a policy framework by the Ministry of Electronics and Information Technology (MeitY) which aims to protect the public and private infrastructure from cyberattacks, and safeguard "information, such as personal information (of web users), financial and banking information and sovereign data". CERT- In is the nodal agency which monitors the cyber threats in the country. The post of National Cyber Security Coordinator has also been created in the Prime Minister's Office (PMO).
The Indian Companies Act 2013 has also introduced cyber law and cyber security obligations on the part of Indian directors. Some provisions for cyber security have been incorporated into rules framed under the Information Technology Act 2000 Update in 2013.[246]
Following cyberattacks in the first half of 2013, when the government, news media, television stations, and bank websites were compromised, the national government committed to the training of 5,000 new cyber security experts by 2017. The South Korean government blamed its northern counterpart for these attacks, as well as incidents that occurred in 2009, 2011,[247] and 2012, but Pyongyang denies the accusations.[248]
In 2016 the National Cyber Security Centre was formed as the central body overseeing cyber-security in the UK, as part of GCHQ.[249][250] The UK government published a National Cyber Security Strategy in 2022 assigning £2.6bn for industry, skills and national security.[251][252] In addition, the National Cyber Force, launched in 2020, works with GCHQ and the Ministry of Defence and aims to "transform the UK’s ability to contest adversaries in cyber space, to protect the country, its people and our way of life".[253]
The United States has its first fully formed cyber plan in 15 years, as a result of the release of this National Cyber plan.[254] In this policy, the US says it will: Protect the country by keeping networks, systems, functions, and data safe; Promote American wealth by building a strong digital economy and encouraging strong domestic innovation; Peace and safety should be kept by making it easier for the US to stop people from using computer tools for bad things, working with friends and partners to do this; and increase the United States' impact around the world to support the main ideas behind an open, safe, reliable, and compatible Internet.[255]
The new U.S. cyber strategy[256] seeks to allay some of those concerns by promoting responsible behavior in cyberspace, urging nations to adhere to a set of norms, both through international law and voluntary standards. It also calls for specific measures to harden U.S. government networks from attacks, like the June 2015 intrusion into the U.S. Office of Personnel Management (OPM), which compromised the records of about 4.2 million current and former government employees. And the strategy calls for the U.S. to continue to name and shame bad cyber actors, calling them out publicly for attacks when possible, along with the use of economic sanctions and diplomatic pressure.[257]
The 1986 18 U.S.C. § 1030, the Computer Fraud and Abuse Act is the key legislation. It prohibits unauthorized access or damage of protected computers as defined in . Although various other measures have been proposed[258][259] – none have succeeded.
In 2013, executive order 13636 Improving Critical Infrastructure Cybersecurity was signed, which prompted the creation of the NIST Cybersecurity Framework.
In response to the Colonial Pipeline ransomware attack[260] President Joe Biden signed Executive Order 14028[261] on May 12, 2021, to increase software security standards for sales to the government, tighten detection and security on existing systems, improve information sharing and training, establish a Cyber Safety Review Board, and improve incident response.
The General Services Administration (GSA) has[when?] standardized the penetration test service as a pre-vetted support service, to rapidly address potential vulnerabilities, and stop adversaries before they impact US federal, state and local governments. These services are commonly referred to as Highly Adaptive Cybersecurity Services (HACS).
The Department of Homeland Security has a dedicated division responsible for the response system, risk management program and requirements for cyber security in the United States called the National Cyber Security Division.[262][263] The division is home to US-CERT operations and the National Cyber Alert System.[263] The National Cybersecurity and Communications Integration Center brings together government organizations responsible for protecting computer networks and networked infrastructure.[264]
The third priority of the FBI is to: "Protect the United States against cyber-based attacks and high-technology crimes",[265] and they, along with the National White Collar Crime Center (NW3C), and the Bureau of Justice Assistance (BJA) are part of the multi-agency task force, The Internet Crime Complaint Center, also known as IC3.[266]
In addition to its own specific duties, the FBI participates alongside non-profit organizations such as InfraGard.[267][268]
The Computer Crime and Intellectual Property Section (CCIPS) operates in the United States Department of Justice Criminal Division. The CCIPS is in charge of investigating computer crime and intellectual property crime and is specialized in the search and seizure of digital evidence in computers and networks.[269] In 2017, CCIPS published A Framework for a Vulnerability Disclosure Program for Online Systems to help organizations "clearly describe authorized vulnerability disclosure and discovery conduct, thereby substantially reducing the likelihood that such described activities will result in a civil or criminal violation of law under the Computer Fraud and Abuse Act (18 U.S.C. § 1030)."[270]
The United States Cyber Command, also known as USCYBERCOM, "has the mission to direct, synchronize, and coordinate cyberspace planning and operations to defend and advance national interests in collaboration with domestic and international partners."[271] It has no role in the protection of civilian networks.[272][273]
The U.S. Federal Communications Commission's role in cyber security is to strengthen the protection of critical communications infrastructure, to assist in maintaining the reliability of networks during disasters, to aid in swift recovery after, and to ensure that first responders have access to effective communications services.[274]
The Food and Drug Administration has issued guidance for medical devices,[275] and the National Highway Traffic Safety Administration[276] is concerned with automotive cyber security. After being criticized by the Government Accountability Office,[277] and following successful attacks on airports and claimed attacks on airplanes, the Federal Aviation Administration has devoted funding to securing systems on board the planes of private manufacturers, and the Aircraft Communications Addressing and Reporting System.[278] Concerns have also been raised about the future Next Generation Air Transportation System.[279]
The US Department of Defense (DoD) issued DoD Directive 8570 in 2004, supplemented by DoD Directive 8140, requiring all DoD employees and all DoD contract personnel involved in information assurance roles and activities to earn and maintain various industry Information Technology (IT) certifications in an effort to ensure that all DoD personnel involved in network infrastructure defense have minimum levels of IT industry recognized knowledge, skills and abilities (KSA). Andersson and Reimers (2019) report these certifications range from CompTIA's A+ and Security+ through the ICS2.org's CISSP, etc.[280]
Computer emergency response team is a name given to expert groups that handle computer security incidents. In the US, two distinct organizations exist, although they do work closely together.
In the context of U.S. nuclear power plants, the U.S. Nuclear Regulatory Commission (NRC) outlines cyber security requirements under 10 CFR Part 73, specifically in §73.54.[282]
The Nuclear Energy Institute's NEI 08-09 document, Cyber Security Plan for Nuclear Power Reactors,[283] outlines a comprehensive framework for cybersecurity in the nuclear power industry. Drafted with input from the U.S. NRC, this guideline is instrumental in aiding licensees to comply with the Code of Federal Regulations (CFR), which mandates robust protection of digital computers and equipment and communications systems at nuclear power plants against cyber threats.[284]
There is growing concern that cyberspace will become the next theater of warfare. As Mark Clayton from The Christian Science Monitor wrote in a 2015 article titled "The New Cyber Arms Race":
In the future, wars will not just be fought by soldiers with guns or with planes that drop bombs. They will also be fought with the click of a mouse a half a world away that unleashes carefully weaponized computer programs that disrupt or destroy critical industries like utilities, transportation, communications, and energy. Such attacks could also disable military networks that control the movement of troops, the path of jet fighters, the command and control of warships.[285]
This has led to new terms such as cyberwarfare and cyberterrorism. The United States Cyber Command was created in 2009[286] and many other countries have similar forces.
There are a few critical voices that question whether cyber security is as significant a threat as it is made out to be.[287][288][289]
Cyber security is a fast-growing field of IT concerned with reducing organizations' risk of getting hacked or data breaches.[290] According to research from the Enterprise Strategy Group, 46% of organizations say that they have a "problematic shortage" of cyber security skills in 2016, up from 28% in 2015.[291] Commercial, government and non-governmental organizations all employ cyber security professionals. The fastest increases in demand for cyber security workers are in industries managing increasing volumes of consumer data such as finance, health care, and retail.[292] However, the use of the term cybersecurity is more prevalent in government job descriptions.[293]
Cyber security job titles and descriptions include:[294]
Student programs are also available for people interested in beginning a career in cyber security.[298][299] Meanwhile, a flexible and effective option for information security professionals of all experience levels to keep studying is online security training, including webcasts.[300][301] A wide range of certified courses are also available.[302]
In the United Kingdom, a nationwide set of cyber security forums, known as the U.K Cyber Security Forum, were established supported by the Government's cyber security strategy[303] in order to encourage start-ups and innovation and to address the skills gap[304] identified by the U.K Government.
In Singapore, the Cyber Security Agency has issued a Singapore Operational Technology (OT) Cybersecurity Competency Framework (OTCCF). The framework defines emerging cyber security roles in Operational Technology. The OTCCF was endorsed by the Infocomm Media Development Authority (IMDA). It outlines the different OT cyber security job positions as well as the technical skills and core competencies necessary. It also depicts the many career paths available, including vertical and lateral advancement opportunities.[305]
The following terms used with regards to computer security are explained below:

Since the Internet's arrival and with the digital transformation initiated in recent years, the notion of cyber security has become a familiar subject in both our professional and personal lives. Cyber security and cyber threats have been consistently present for the last 60 years of technological change. In the 1970s and 1980s, computer security was mainly limited to academia until the conception of the Internet, where, with increased connectivity, computer viruses and network intrusions began to take off. After the spread of viruses in the 1990s, the 2000s marked the institutionalization of organized attacks such as distributed denial of service.[309] This led to the formalization of cyber security as a professional discipline.[310]
The April 1967 session organized by Willis Ware at the Spring Joint Computer Conference, and the later publication of the Ware Report, were foundational moments in the history of the field of computer security.[311] Ware's work straddled the intersection of material, cultural, political, and social concerns.[311]
A 1977 NIST publication[312] introduced the CIA triad of confidentiality, integrity, and availability as a clear and simple way to describe key security goals.[313] While still relevant, many more elaborate frameworks have since been proposed.[314][315]
However, in the 1970s and 1980s, there were no grave computer threats because computers and the internet were still in the early stages of development, and security threats were easily identifiable. More often, threats came from malicious insiders who gained unauthorized access to sensitive documents and files. Although malware and network breaches existed during the early years, they did not use them for financial gain. By the second half of the 1970s, established computer firms like IBM started offering commercial access control systems and computer security software products.[316]
One of the earliest examples of an attack on a computer network was the computer worm Creeper written by Bob Thomas at BBN, which propagated through the ARPANET in 1971.[317] The program was purely experimental in nature and carried no malicious payload. A later program, Reaper, was created by Ray Tomlinson in 1972 and used to destroy Creeper.[318]
Between September 1986 and June 1987, a group of German hackers performed the first documented case of cyber espionage.[319] The group hacked into American defense contractors, universities, and military base networks and sold gathered information to the Soviet KGB. The group was led by Markus Hess, who was arrested on 29 June 1987. He was convicted of espionage (along with two co-conspirators) on 15 Feb 1990.
In 1988, one of the first computer worms, called the Morris worm, was distributed via the Internet. It gained significant mainstream media attention.[320]
Netscape started developing the protocol SSL, shortly after the National Center for Supercomputing Applications (NCSA) launched Mosaic 1.0, the first web browser, in 1993.[321][322] Netscape had SSL version 1.0 ready in 1994, but it was never released to the public due to many serious security vulnerabilities.[321] However, in 1995, Netscape launched Version 2.0.[323]
The National Security Agency (NSA) is responsible for the protection of U.S. information systems and also for collecting foreign intelligence.[324] The agency analyzes commonly used software and system configurations to find security flaws, which it can use for offensive purposes against competitors of the United States.[325]
NSA contractors created and sold click-and-shoot attack tools to US agencies and close allies, but eventually, the tools made their way to foreign adversaries.[326] In 2016, NSAs own hacking tools were hacked, and Russia and North Korea have used it.[327] NSA's employees and contractors have been recruited at high salaries by adversaries, anxious to compete in cyberwarfare.[328] In 2007, the United States and Israel began exploiting security flaws in the Microsoft Windows operating system to attack and damage equipment used in Iran to refine nuclear materials. Iran responded by heavily investing in their own cyberwarfare capability, which it began using against the United States.[325]
citation: CS1 maint: work parameter with ISBN (link)network vulnerability scans at least quarterly and after any significant change in the network
Exclusive: Top secret court order requiring Verizon to hand over all call data shows scale of domestic surveillance under Obama
cite news: CS1 maint: deprecated archival service (link)
|
United States of America
|
|||
|---|---|---|---|
| Motto: "In God We Trust"[1]
Other traditional mottos:[2]
|
|||
| Anthem: "The Star-Spangled Banner"[3]
|
|||
| Capital | Washington, D.C. 38°53′N 77°1′W / 38.883°N 77.017°W |
||
| Largest city | New York City | 40°43′N 74°0′W / 40.717°N 74.000°W | |
| Official languages | English[a] | ||
| Ethnic groups |
By race:
|
||
| Religion
(2025)[9]
|
|||
| Demonym | American[10][b] | ||
| Government | Federal presidential republic | ||
| Donald Trump | |||
| JD Vance | |||
| Mike Johnson | |||
| John Roberts | |||
| Legislature | Congress | ||
| Senate | |||
| House of Representatives | |||
| Independence
from Great Britain
|
|||
| July 4, 1776 | |||
| March 1, 1781 | |||
| September 3, 1783 | |||
| March 4, 1789 | |||
| Area | |||
|
• Total area
|
3,796,742 sq mi (9,833,520 km2)[12][c] (3rd) | ||
|
• Water (%)
|
7.0[11] (2010) | ||
|
• Land area
|
3,531,905 sq mi (9,147,590 km2) (3rd) | ||
| Population | |||
|
• 2025 estimate
|
|||
|
• 2020 census
|
|||
|
• Density
|
96.8/sq mi (37.4/km2) (180th) | ||
| GDP | (PPP) | 2025 estimate | |
|
• Total
|
|||
|
• Per capita
|
|||
| GDP | (nominal) | 2025 estimate | |
|
• Total
|
|||
|
• Per capita
|
|||
| Gini | (2024) | medium inequality |
|
| HDI | (2023) | very high (17th) | |
| Currency | U.S. dollar ($) (USD) | ||
| Time zone | UTC−4 to −12, +10, +11 | ||
|
• Summer (DST)
|
UTC−4 to −10[g] | ||
| Date format | mm/dd/yyyy[h] | ||
| Calling code | +1 | ||
| ISO 3166 code | US | ||
| Internet TLD | .com, .us[18] | ||
The United States of America (USA), also known as the United States (U.S.) or America, is a country primarily located in North America. It is a federal republic of 50 states and a federal capital district, Washington, D.C. The 48 contiguous states border Canada to the north and Mexico to the south, with the semi-exclave of Alaska in the northwest and the archipelago of Hawaii in the Pacific Ocean. The United States also asserts sovereignty over five major island territories and various uninhabited islands in Oceania and the Caribbean.[j] It is a megadiverse country, with the world's third-largest land area[c] and third-largest population, exceeding 341 million.[k]
Paleo-Indians first migrated from North Asia to North America at least 15,000 years ago, and formed various civilizations. Spanish colonization established Spanish Florida in 1513, the first European colony in what is now the continental United States. British colonization followed with the 1607 settlement of Virginia, the first of the Thirteen Colonies. Enslavement of Africans was practiced in every colony and supplied most of the labor for the Southern Colonies' plantation economy. Clashes with the British Crown began as a civil protest over the illegality of taxation without representation in Parliament and the denial of other English rights. They evolved into the American Revolution, which led to the Declaration of Independence and a society based on universal rights. Victory in the 1775–1783 Revolutionary War brought international recognition of U.S. sovereignty and fueled westward expansion, further dispossessing native inhabitants. As more states were admitted into the Union, a North–South division over slavery led 11 Southern states to attempt to secede and join as the Confederate States of America, which fought against the Union in the American Civil War of 1861–1865. With the United States' victory and reunification, slavery was abolished nationally. By 1900, the country had established itself as a great power, a status solidified after its involvement in World War I. Following Japan's attack on Pearl Harbor in 1941, the U.S. entered World War II. Its aftermath left the U.S. and the Soviet Union as rival superpowers, competing for ideological dominance and international influence during the Cold War. The collapse of the Soviet Union in 1991 ended the Cold War, leaving the U.S. as the world's sole superpower. After the terror attacks of September 11, 2001, the U.S. launched the war on terror, invading Afghanistan and Iraq. It has continued carrying out numerous foreign interventions since then.
The U.S. federal government is a representative democracy with a president and a constitution that creates a separation of powers among three branches: legislative, executive, and judicial. The United States Congress is a bicameral national legislature composed of the House of Representatives (a lower house based on population) and the Senate (an upper house based on equal representation for each state). Federalism grants substantial autonomy to the 50 states. In addition, 574 Native American tribes have sovereignty rights, and there are 326 Native American reservations. Since the 1850s, the Democratic and Republican parties have dominated American politics. American ideals and values are based on a democratic tradition inspired by the American Enlightenment movement.
A developed country, the U.S. ranks high in economic competitiveness, innovation, and higher education. Accounting for over a quarter of nominal global GDP, its economy has been the world's largest since about 1890. It is the wealthiest country, with the highest disposable household income per capita among OECD members, though its wealth inequality is highly pronounced. Shaped by centuries of immigration, the culture of the U.S. is diverse and globally influential. Making up more than a third of global military spending, the country is widely considered to have the most powerful armed forces in the world and was the first to develop nuclear weapons. A member of numerous international organizations including the United Nations Security Council, the U.S. plays a major role in global political, cultural, economic, and military affairs.
Documented use of the phrase "United States of America" dates back to January 2, 1776. On that day, Stephen Moylan, a Continental Army aide to General George Washington, wrote a letter to Joseph Reed, Washington's aide-de-camp, seeking to go "with full and ample powers from the United States of America to Spain" to seek assistance in the Revolutionary War effort.[22][23] The first known public usage is an anonymous essay published in the Williamsburg newspaper The Virginia Gazette on April 6, 1776.[22] Sometime on or after June 11, 1776, Thomas Jefferson wrote "United States of America" in a rough draft of the Declaration of Independence,[22] which was adopted by the Second Continental Congress on July 4, 1776.[24]
The term "United States" and its initialism "U.S.", used as nouns or as adjectives in English, are common short names for the country. The initialism "USA", a noun, is also common.[25] "United States" and "U.S." are the established terms throughout the U.S. federal government, with prescribed rules.[l] "The States" is an established colloquial shortening of the name, used particularly from abroad;[27] "stateside" is the corresponding adjective or adverb.[28]
" America" is the feminine form of the first name of Americus Vesputius, the Latinized name of Italian explorer Amerigo Vespucci (1454–1512);[m] It was first used as a place name by the German cartographers Martin Waldseemüller and Matthias Ringmann in 1507.[29][n] Vespucci first proposed that the West Indies discovered by Christopher Columbus in 1492 were part of a previously unknown landmass and not among the Indies at the eastern limit of Asia.[30][31][32] In English, the term "America" (used without a qualifier) seldom refers to topics unrelated to the United States. "The Americas" is the general term to describe the totality of the continents of North and South America.[33]

The first inhabitants of North America migrated from Siberia approximately 15,000 years ago, either across the Bering land bridge or along the now-submerged Ice Age coastline.[35][36] Small isolated groups of hunter-gatherers are said to have migrated alongside herds of large herbivores far into Alaska, with ice-free corridors developing along the Pacific coast and valleys of North America in c. 16,500 – c. 13,500 BCE (c. 18,500 – c. 15,500 BP).[37] The Clovis culture, which appeared around 11,000 BCE, is believed to be the first widespread culture in the Americas.[38][39] Over time, Indigenous North American cultures grew increasingly sophisticated, and some, such as the Mississippian culture, developed agriculture, architecture, and complex societies.[40] In the post-archaic period, the Mississippian cultures were located in the midwestern, eastern, and southern regions, and the Algonquian in the Great Lakes region and along the Eastern Seaboard, while the Hohokam culture and Ancestral Puebloans inhabited the Southwest.[41] Native population estimates of what is now the United States before the arrival of European colonizers range from around 500,000[42][43] to nearly 10 million.[43][44]

Christopher Columbus began exploring the Caribbean for Spain in 1492, leading to Spanish-speaking settlements and missions from what are now Puerto Rico and Florida to New Mexico and California. The first Spanish colony in the present-day continental United States was Spanish Florida, chartered in 1513.[45][46][47][48] After several settlements failed there due to starvation and disease, Spain's first permanent town, Saint Augustine, was founded in 1565.[49]
France established its own settlements in French Florida in 1562, but they were either abandoned (Charlesfort, 1578) or destroyed by Spanish raids (Fort Caroline, 1565). Permanent French settlements were founded much later along the Great Lakes (Fort Detroit, 1701), the Mississippi River (St. Louis, 1764) and especially the Gulf of Mexico (New Orleans, 1718).[50] Early European colonies also included the thriving Dutch colony of New Nederland (settled 1626, present-day New York) and the small Swedish colony of New Sweden (settled 1638 in what became Delaware). British colonization of the East Coast began with the Virginia Colony (1607) and the Plymouth Colony (Massachusetts, 1620).[51][52]
The Mayflower Compact in Massachusetts and the Fundamental Orders of Connecticut established precedents for local representative self-governance and constitutionalism that would develop throughout the American colonies.[53][54] While European settlers in what is now the United States experienced conflicts with Native Americans, they also engaged in trade, exchanging European tools for food and animal pelts.[55][o] Relations ranged from close cooperation to warfare and massacres. The colonial authorities often pursued policies that forced Native Americans to adopt European lifestyles, including conversion to Christianity.[59][60] Along the eastern seaboard, settlers trafficked Africans through the Atlantic slave trade, largely to provide manual labor on plantations.[61]
The original Thirteen Colonies[p] that would later found the United States were administered as possessions of the British Empire by Crown-appointed governors,[62] though local governments held elections open to most white male property owners.[63][64] The colonial population grew rapidly from Maine to Georgia, eclipsing Native American populations;[65] by the 1770s, the natural increase of the population was such that only a small minority of Americans had been born overseas.[66] The colonies' distance from Britain facilitated the entrenchment of self-governance,[67] and the First Great Awakening, a series of Christian revivals, fueled colonial interest in guaranteed religious liberty.[68]

Following its victory in the French and Indian War, Britain began to assert greater control over local affairs in the Thirteen Colonies, resulting in growing political resistance. One of the primary grievances of the colonists was the denial of their rights as Englishmen, particularly the right to representation in the British government that taxed them. To demonstrate their dissatisfaction and resolve, the First Continental Congress met in 1774 and passed the Continental Association, a colonial boycott of British goods enforced by local "committees of safety" that proved effective. The British attempt to then disarm the colonists resulted in the 1775 Battles of Lexington and Concord, igniting the American Revolutionary War. At the Second Continental Congress, the colonies appointed George Washington commander-in-chief of the Continental Army, and created a committee that named Thomas Jefferson to draft the Declaration of Independence. Two days after the Second Continental Congress passed the Lee Resolution to create an independent, sovereign nation, the Declaration was adopted on July 4, 1776.[69] The political values of the American Revolution evolved from an armed rebellion demanding reform within an empire to a revolution that created a new social and governing system founded on the defense of liberty and the protection of inalienable natural rights; sovereignty of the people;[70] republicanism over monarchy, aristocracy, and other hereditary political power; civic virtue; and an intolerance of political corruption.[71] The Founding Fathers of the United States, who included Washington, Jefferson, John Adams, Benjamin Franklin, Alexander Hamilton, John Jay, James Madison, Thomas Paine, and many others, were inspired by Classical, Renaissance, and Enlightenment philosophies and ideas.[72][73]
Though in practical effect since its drafting in 1777, the Articles of Confederation was ratified in 1781 and formally established a decentralized government that operated until 1789.[69] After the British surrender at the siege of Yorktown in 1781, American sovereignty was internationally recognized by the Treaty of Paris (1783), through which the U.S. gained territory stretching west to the Mississippi River, north to present-day Canada, and south to Spanish Florida.[74] The Northwest Ordinance (1787) established the precedent by which the country's territory would expand with the admission of new states, rather than the expansion of existing states.[75]
The U.S. Constitution was drafted at the 1787 Constitutional Convention to overcome the limitations of the Articles. It went into effect in 1789, creating a federal republic governed by three separate branches that together formed a system of checks and balances.[76] George Washington was elected the country's first president under the Constitution, and the Bill of Rights was adopted in 1791 to allay skeptics' concerns about the power of the more centralized government.[77] His resignation as commander-in-chief after the Revolutionary War and his later refusal to run for a third term as the country's first president established a precedent for the supremacy of civil authority in the United States and the peaceful transfer of power.[78]

In the late 18th century, American settlers began to expand westward in larger numbers, many with a sense of manifest destiny.[79][80] The Louisiana Purchase of 1803 from France nearly doubled the territory of the United States.[81][82] Lingering issues with Britain remained, leading to the War of 1812, which was fought to a draw.[83] Spain ceded Florida and its Gulf Coast territory in 1819.[84]
The Missouri Compromise of 1820, which admitted Missouri as a slave state and Maine as a free state, attempted to balance the desire of northern states to prevent the expansion of slavery into new territories with that of southern states to extend it there. Primarily, the compromise prohibited slavery in all other lands of the Louisiana Purchase north of the 36°30′ parallel.[85]
As Americans expanded further into territory inhabited by Native Americans, the federal government implemented policies of Indian removal or assimilation.[86][87] The most significant such legislation was the Indian Removal Act of 1830, a key policy of President Andrew Jackson. It resulted in the Trail of Tears (1830–1850), in which an estimated 60,000 Native Americans living east of the Mississippi River were forcibly removed and displaced to lands far to the west, causing 13,200 to 16,700 deaths along the forced march.[88] Settler expansion as well as this influx of Indigenous peoples from the East resulted in the American Indian Wars west of the Mississippi.[89][90]
During the colonial period, slavery became legal in all the Thirteen colonies, and by 1770 it provided the main labor force in the large-scale, agriculture-dependent economies of the Southern Colonies from Maryland to Georgia. The practice began to be significantly questioned during the American Revolution,[91] and spurred by an active abolitionist movement that had reemerged in the 1830s, states in the North enacted laws to prohibit slavery within their boundaries.[92] At the same time, support for slavery had strengthened in Southern states, with widespread use of inventions such as the cotton gin (1793) having made slavery immensely profitable for Southern elites.[93][94][95]
The United States annexed the Republic of Texas in 1845,[96] and the 1846 Oregon Treaty led to U.S. control of the present-day American Northwest.[97] Dispute with Mexico over Texas led to the Mexican–American War (1846–1848). After the victory of the U.S., Mexico recognized U.S. sovereignty over Texas, New Mexico, and California in the 1848 Mexican Cession; the cession's lands also included the future states of Nevada, Colorado and Utah.[79][98] The California gold rush of 1848–1849 spurred a huge migration of white settlers to the Pacific coast, leading to even more confrontations with Native populations. One of the most violent, the California genocide of thousands of Native inhabitants, lasted into the mid-1870s.[99] Additional western territories and states were created.[100]

Throughout the 1850s, the sectional conflict regarding slavery was further inflamed by national legislation in the U.S. Congress and decisions of the Supreme Court. In Congress, the Fugitive Slave Act of 1850 mandated the forcible return to their owners in the South of slaves taking refuge in non-slave states, while the Kansas–Nebraska Act of 1854 effectively gutted the anti-slavery requirements of the Missouri Compromise.[101] In its Dred Scott decision of 1857, the Supreme Court ruled against a slave brought into non-slave territory, simultaneously declaring the entire Missouri Compromise to be unconstitutional. These and other events exacerbated tensions between North and South that would culminate in the American Civil War (1861–1865).[102][103]
Beginning with South Carolina, 11 slave-state governments voted to secede from the United States in 1861, joining to create the Confederate States of America. All other state governments remained loyal to the Union.[q][104][105] War broke out in April 1861 after the Confederacy bombarded Fort Sumter.[106][107] Following the Emancipation Proclamation on January 1, 1863, many freed slaves joined the Union army.[108] The war began to turn in the Union's favor following the 1863 Siege of Vicksburg and Battle of Gettysburg, and the Confederates surrendered in 1865 after the Union's victory in the Battle of Appomattox Court House.[109]
Efforts toward reconstruction in the secessionist South had begun as early as 1862,[112] but it was only after President Lincoln's assassination that the three Reconstruction Amendments to the Constitution were ratified to protect civil rights. The amendments codified nationally the abolition of slavery and involuntary servitude except as punishment for crimes, promised equal protection under the law for all persons, and prohibited discrimination on the basis of race or previous enslavement.[113][114][115] As a result, African Americans took an active political role in ex-Confederate states in the decade following the Civil War.[116][117] The former Confederate states were readmitted to the Union, beginning with Tennessee in 1866 and ending with Georgia in 1870.[118][119]
National infrastructure, including transcontinental telegraph and railroads, spurred growth in the American frontier. This was accelerated by the Homestead Acts, through which nearly 10 percent of the total land area of the United States was given away free to some 1.6 million homesteaders.[120][121] From 1865 through 1917, an unprecedented stream of immigrants arrived in the United States, including 24.4 million from Europe.[122] Most came through the Port of New York, as New York City and other large cities on the East Coast became home to large Jewish, Irish, and Italian populations. Many Northern Europeans as well as significant numbers of Germans and other Central Europeans moved to the Midwest. At the same time, about one million French Canadians migrated from Quebec to New England.[123] During the Great Migration, millions of African Americans left the rural South for urban areas in the North.[124] Alaska was purchased from Russia in 1867.[125]
The Compromise of 1877 is generally considered the end of the Reconstruction era, as it resolved the electoral crisis following the 1876 presidential election and led President Rutherford B. Hayes to reduce the role of federal troops in the South.[126] Immediately, the Redeemers began evicting the Carpetbaggers and quickly regained local control of Southern politics in the name of white supremacy.[127][128] African Americans endured a period of heightened, overt racism following Reconstruction, a time often considered the nadir of American race relations.[129][130] A series of Supreme Court decisions, including Plessy v. Ferguson, emptied the Fourteenth and Fifteenth Amendments of their force, allowing Jim Crow laws in the South to remain unchecked, sundown towns in the Midwest, and segregation in communities across the country, which would be reinforced in part by the policy of redlining later adopted by the federal Home Owners' Loan Corporation.[131]
An explosion of technological advancement, accompanied by the exploitation of cheap immigrant labor,[132] led to rapid economic expansion during the Gilded Age of the late 19th century. It continued into the early 20th, when the United States already outpaced the economies of Britain, France, and Germany combined. Tycoons led the nation's expansion in the railroad, petroleum, and steel industries, as the United States emerged as a pioneer of the automotive industry.[133][134][135][136] This fostered the amassing of enormous economic and political power by a few prominent industrialists, largely through the formation of trusts and monopolies to prevent competition.[137] These changes resulted in significant increases in economic inequality, slum conditions, and social unrest, creating a fertile environment for labor unions and socialist movements to flourish.[138][139][140] This period eventually ended with the advent of the Progressive Era, which was characterized by significant economic and social reforms.[141][142]
Pro-American elements in Hawaii overthrew the Hawaiian monarchy; the islands were annexed in 1898. That same year, Puerto Rico, the Philippines, and Guam were ceded to the U.S. by Spain after the latter's defeat in the Spanish–American War. (The Philippines was granted full independence from the U.S. on July 4, 1946, following World War II. Puerto Rico and Guam have remained U.S. territories.)[143] American Samoa was acquired by the United States in 1900 after the Second Samoan Civil War.[144] The U.S. Virgin Islands were purchased from Denmark in 1917 after Danish voters approved the sale in a 1916 referendum.[145]

The United States entered World War I alongside the Allies in 1917 helping to turn the tide against the Central Powers.[146] In 1920, a constitutional amendment granted nationwide women's suffrage.[147] During the 1920s and 1930s, radio for mass communication and early television transformed communications nationwide.[148] The Wall Street Crash of 1929 triggered the Great Depression, to which President Franklin D. Roosevelt responded with the New Deal plan of "reform, recovery and relief", a series of unprecedented and sweeping recovery programs and employment relief projects combined with financial reforms and regulations.[149][150]
Initially neutral during World War II, the U.S. began supplying war materiel to the Allies of World War II in March 1941 and entered the war in December after Japan's attack on Pearl Harbor.[151] Agreeing to a "Europe first" policy, the U.S. concentrated its wartime efforts on Japan's allies Italy and Germany until their final defeat in May 1945. The U.S. developed the first nuclear weapons and used them against the Japanese cities of Hiroshima and Nagasaki in August 1945, ending the war.[152][153] The United States was one of the "Four Policemen" who met to plan the post-war world, alongside the United Kingdom, the Soviet Union, and China.[154][155] The U.S. emerged relatively unscathed from the war, with even greater economic power and international political influence.[156]

The end of World War II in 1945 left the U.S. and the Soviet Union as superpowers, each with its own political, military, and economic sphere of influence. Geopolitical tensions between the two superpowers soon led to the Cold War.[157][158][159] The U.S. implemented a policy of containment intended to limit the Soviet Union's sphere of influence; engaged in regime change against governments perceived to be aligned with the Soviets; and prevailed in the Space Race, which culminated with the first crewed Moon landing in 1969.[160][161]
Domestically, the U.S. experienced economic growth, urbanization, and population growth following World War II.[162] The civil rights movement emerged, with Martin Luther King Jr. becoming a prominent leader in the early 1960s.[163] The Great Society plan of President Lyndon B. Johnson's administration resulted in groundbreaking and broad-reaching laws, policies and a constitutional amendment to counteract some of the worst effects of lingering institutional racism.[164]
The counterculture movement in the U.S. brought significant social changes, including the liberalization of attitudes toward recreational drug use and sexuality.[165][166] It also encouraged open defiance of the military draft (leading to the end of conscription in 1973)[167] and wide opposition to U.S. intervention in Vietnam, with the U.S. totally withdrawing in 1975.[168] A societal shift in the roles of women was significantly responsible for the large increase in female paid labor participation starting in the 1970s, and by 1985 the majority of American women aged 16 and older were employed.[169]
The Fall of Communism and the dissolution of the Soviet Union from 1989 to 1991 marked the end of the Cold War and left the United States as the world's sole superpower.[170][171][172][173][174] This cemented the United States' global influence, reinforcing the concept of the "American Century" as the U.S. dominated international political, cultural, economic, and military affairs.[175][176]

The 1990s saw the longest recorded economic expansion in American history, a dramatic decline in U.S. crime rates, and advances in technology. Throughout this decade, technological innovations such as the World Wide Web, the evolution of the Pentium microprocessor in accordance with Moore's law, rechargeable lithium-ion batteries, the first gene therapy trial, and cloning either emerged in the U.S. or were improved upon there. The Human Genome Project was formally launched in 1990, while Nasdaq became the first stock market in the United States to trade online in 1998.[177]
In the Gulf War of 1991, an American-led international coalition of states expelled an Iraqi invasion force that had occupied neighboring Kuwait.[178] The September 11 attacks on the United States in 2001 by the pan-Islamist militant organization al-Qaeda led to the war on terror and subsequent military interventions in Afghanistan and in Iraq.[179][180][181]
The U.S. housing bubble culminated in 2007 with the Great Recession, the largest economic contraction since the Great Depression.[182] Beginning in the 2010s, and particularly in the 2020s, the United States has experienced increased political polarization[183][184] and democratic backsliding.[185][186] The country's polarization was violently reflected in the January 2021 Capitol attack,[187] when a mob of insurrectionists[188] entered the U.S. Capitol and sought to prevent the peaceful transfer of power[189] in an attempted self-coup d'état.[190]

The United States is the world's third-largest country by total area behind Russia and Canada.[c] The 48 contiguous states and the District of Columbia have a combined area of 3,119,885 square miles (8,080,470 km2).[12][191] In 2021, the United States had 8% of the Earth's permanent meadows and pastures and 10% of its cropland.[192]
Starting in the east, the coastal plain of the Atlantic seaboard gives way to inland forests and rolling hills in the Piedmont plateau region.[193] The Appalachian Mountains and the Adirondack Massif separate the East Coast from the Great Lakes and the grasslands of the Midwest.[194] The Mississippi River System, the world's fourth-longest river system, runs predominantly north–south through the center of the country. The flat and fertile prairie of the Great Plains stretches to the west, interrupted by a highland region in the southeast.[194]

The Rocky Mountains, west of the Great Plains, extend north to south across the country, peaking at over 14,000 feet (4,300 m) in Colorado.[195] The supervolcano underlying Yellowstone National Park in the Rocky Mountains, the Yellowstone Caldera, is the continent's largest volcanic feature.[196] Farther west are the rocky Great Basin and the Chihuahuan, Sonoran, and Mojave deserts.[197] In the northwest corner of Arizona, carved by the Colorado River, is the Grand Canyon, a steep-sided canyon and popular tourist destination[198] known for its overwhelming visual size and intricate, colorful landscape. The Cascade and Sierra Nevada mountain ranges run close to the Pacific coast. The lowest and highest points in the contiguous United States are in the State of California,[199] about 84 miles (135 km) apart.[200]
At an elevation of 20,310 feet (6,190.5 m), Alaska's Denali (also called Mount McKinley) is the highest peak in the country and on the continent.[201] Active volcanoes in the U.S. are common throughout Alaska's Alexander and Aleutian Islands. Located entirely outside North America, the archipelago of Hawaii consists of volcanic islands, physiographically and ethnologically part of the Polynesian subregion of Oceania.[202]
In addition to its total land area, the United States has one of the world's largest marine exclusive economic zones spanning approximately 4.5 million square miles (11.7 million km2) of ocean.[203][204]

With its large size and geographic variety, the United States includes most climate types. East of the 100th meridian, the climate ranges from humid continental in the north to humid subtropical in the south.[205] The western Great Plains are semi-arid.[206] Many mountainous areas of the American West have an alpine climate. The climate is arid in the Southwest, Mediterranean in coastal California, and oceanic in coastal Oregon, Washington, and southern Alaska. Most of Alaska is subarctic or polar. Hawaii, the southern tip of Florida and U.S. territories in the Caribbean and Pacific are tropical.[207]
The United States receives more high-impact extreme weather incidents than any other country.[208][209] States bordering the Gulf of Mexico are prone to hurricanes, and most of the world's tornadoes occur in the country, mainly in Tornado Alley.[210] Due to climate change in the country, extreme weather has become more frequent in the U.S. in the 21st century, with three times the number of reported heat waves compared to the 1960s.[211][212][213] Since the 1990s, droughts in the American Southwest have become more persistent and more severe.[214] The regions considered as the most attractive to the population are the most vulnerable.[215]

The U.S. is one of 17 megadiverse countries containing large numbers of endemic species: about 17,000 species of vascular plants occur in the contiguous United States and Alaska, and over 1,800 species of flowering plants are found in Hawaii, few of which occur on the mainland.[217] The United States is home to 428 mammal species, 784 birds, 311 reptiles, 295 amphibians,[218] and around 91,000 insect species.[219]
There are 63 national parks, and hundreds of other federally managed monuments, forests, and wilderness areas, administered by the National Park Service and other agencies.[220] About 28% of the country's land is publicly owned and federally managed,[221] primarily in the Western States.[222] Most of this land is protected, though some is leased for commercial use, and less than one percent is used for military purposes.[223][224]
Environmental issues in the United States include debates on non-renewable resources and nuclear energy, air and water pollution, biodiversity, logging and deforestation,[225][226] and climate change.[227][228] The U.S. Environmental Protection Agency (EPA) is the federal agency charged with addressing most environmental-related issues.[229] The idea of wilderness has shaped the management of public lands since 1964, with the Wilderness Act.[230] The Endangered Species Act of 1973 provides a way to protect threatened and endangered species and their habitats. The United States Fish and Wildlife Service implements and enforces the Act.[231] In 2024, the U.S. ranked 35th among 180 countries in the Environmental Performance Index.[232]
The United States is a federal republic of 50 states and a federal capital district, Washington, D.C. The U.S. asserts sovereignty over five unincorporated territories and several uninhabited island possessions.[19][233] It is the world's oldest surviving federation,[234] and its presidential system of federal government has been adopted, in whole or in part, by many newly independent states worldwide following their decolonization.[235] The Constitution of the United States serves as the country's supreme legal document.[236] Most scholars describe the United States as a liberal democracy,[237] though some have used descriptions such as oligarchy or plutocracy instead.[r]
Composed of three branches, all headquartered in Washington, D.C., the federal government is the national government of the United States. The U.S. Constitution establishes a separation of powers intended to provide a system of checks and balances to prevent any of the three branches from becoming supreme.[249]
The U.S. Congress is a bicameral legislature made up of the Senate and the House of Representatives. The Senate has 100 members—two residents from each state and elected by that state's voters for a six-year term. The House of Representatives has 435 members, elected for a two-year term by the constituency of the congressional district where they reside. A state's legislature decides the district boundaries, which are contiguous within the state. Every U.S. congressional district is of equivalent population and sends one representative to Congress.[250] Election years for senators are staggered so that only one-third of them will be up for election every two years.[251] U.S. representatives are all up for election at the same time every two years. The U.S. Congress makes federal law, declares war, approves treaties, has the power of the purse,[252] and has the power of impeachment.[253] One of its foremost non-legislative functions is the power to investigate and oversee the executive branch.[254] Congressional oversight is usually delegated to committees and is facilitated by Congress's power to issue subpoenas.[255] Much of the work of Congress is performed by a collection of committees, each appointed for a specific purpose or function. Committee membership is by tradition and statute bipartisan, but all committees are chaired by a member of the majority party, who sets the committee agenda.[256]
The U.S. president is the head of state, commander-in-chief of the military, and chief executive of the federal government. The president appoints the members of the Cabinet, subject to Senate approval, and names other officials who administer and enforce federal law and policy through their respective agencies.[257] The president has the ability to veto legislative bills from the U.S. Congress before they become law. However, presidential vetoes can be overridden by a two-thirds supermajority vote in both chambers of Congress. The president also has clemency power for federal crimes and can issue pardons. Finally, the president has the authority to issue expansive "executive orders" in a number of policy areas, subject to judicial review. Candidates for president campaign with a vice-presidential running mate. Both candidates are elected together, or defeated together, in a presidential election. Unlike other votes in American politics, this is technically an indirect election in which the winner will be determined by the U.S. Electoral College. There, votes are officially cast by individual electors selected by their state legislature.[258] In practice, however, each of the 50 states chooses a group of presidential electors who are required by state law to confirm the winner of their state's popular vote. Each state is allocated two electors plus one additional elector for every congressional district in the state, which in effect combines to equal the number of elected officials that state sends to Congress. The District of Columbia, with no representatives or senators, is allocated three electoral votes. Both the president and the vice president serve a four-year term, and the president may be reelected to the office only once, for one additional four-year term.[s]
The U.S. federal judiciary, whose judges are all appointed for life by the president with Senate approval, consists primarily of the U.S. Supreme Court, the U.S. courts of appeals, and the U.S. district courts. The lowest level in the federal judiciary is the federal district court, which decides all cases considered to be under "original jurisdiction", such as federal statutes, constitutional law, or international treaties. After a federal district court has decided a case, its decision may be contested and sent to a higher court, a federal court of appeals. The U.S. judicial system's 12 federal circuits divide the country into 12 separate geographic administrative regions for appeals decisions. The next and highest court in the system is the Supreme Court of the United States.[259] The U.S. Supreme Court interprets laws and overturns those it finds unconstitutional.[259] On average, the Supreme Court receives about 7,000 appeals petitions for writs of certiorari each year, but only grants about 80.[260] Consisting of nine members led by the Chief Justice of the United States, the court judges each case before it by majority decision. As with all other federal judges, the members are appointed for life by the sitting president with Senate approval when a vacancy becomes available.[261]
The three-branch system is known as the presidential system, in contrast to the parliamentary system where the executive is part of the legislative body. Many countries around the world adopted this aspect of the 1789 Constitution of the United States, especially in the postcolonial Americas.[262]

In the U.S. federal system, sovereign powers are shared between three levels of government specified in the Constitution: the federal government, the states, and Indian tribes.[263][264] The U.S. also asserts sovereignty over five permanently inhabited territories: American Samoa, Guam, the Northern Mariana Islands, Puerto Rico, and the U.S. Virgin Islands.[19]
Residents of the 50 states are governed by their elected state government, under state constitutions compatible with the national constitution, and by elected local governments that are administrative divisions of a state.[265] States are subdivided into counties or county equivalents, and (except for Hawaii) further divided into municipalities, each administered by elected representatives. The District of Columbia is a federal district containing the U.S. capital, Washington, D.C.[266] The federal district is an administrative division of the federal government.[267]

Indian country is made up of 574 federally recognized tribes and 326 Indian reservations. They hold a government-to-government relationship with the U.S. federal government in Washington and are legally defined as domestic dependent nations with inherent tribal sovereignty rights.[264][263][268][269]
In addition to the five major territories, the U.S. also asserts sovereignty over the United States Minor Outlying Islands in the Pacific Ocean and the Caribbean.[19] The seven undisputed islands without permanent populations are Baker Island, Howland Island, Jarvis Island, Johnston Atoll, Kingman Reef, Midway Atoll, and Palmyra Atoll. U.S. sovereignty over the unpopulated Bajo Nuevo Bank, Navassa Island, Serranilla Bank, and Wake Island is disputed.[19]


The Constitution is silent on political parties. However, they developed independently in the 18th century with the Federalist and Anti-Federalist parties.[270] Since then, the United States has operated as a de facto two-party system, though the parties have changed over time.[271] Since the mid-19th century, the two main national parties have been the Democratic Party and the Republican Party. The former is perceived as relatively liberal in its political platform while the latter is perceived as relatively conservative in its platform.[272]

The United States has an established structure of foreign relations, with the world's second-largest diplomatic corps as of 2024[update]. It is a permanent member of the United Nations Security Council[273] and home to the United Nations headquarters.[274] The United States is a member of the G7,[275] G20,[276] and OECD intergovernmental organizations.[277] Almost all countries have embassies and many have consulates (official representatives) in the country. Likewise, nearly all countries host formal diplomatic missions with the United States, except Iran,[278] North Korea,[279] and Bhutan.[280] Though Taiwan does not have formal diplomatic relations with the U.S., it maintains close unofficial relations.[281] The United States regularly supplies Taiwan with military equipment to deter potential Chinese aggression.[282] Its geopolitical attention also turned to the Indo-Pacific when the United States joined the Quadrilateral Security Dialogue with Australia, India, and Japan.[283]
The United States has a "Special Relationship" with the United Kingdom[284] and strong ties with Canada,[285] Australia,[286] New Zealand,[287] the Philippines,[288] Japan,[289] South Korea,[290] Israel,[291] and several European Union countries such as France, Italy, Germany, Spain, and Poland.[292] The U.S. works closely with its NATO allies on military and national security issues, and with countries in the Americas through the Organization of American States and the United States–Mexico–Canada Free Trade Agreement. The U.S. exercises full international defense authority and responsibility for Micronesia, the Marshall Islands, and Palau through the Compact of Free Association.[259] It has increasingly conducted strategic cooperation with India,[293] while its ties with China have steadily deteriorated.[294][295] Beginning in 2014, the U.S. had become a key ally of Ukraine.[296][297]

The president is the commander-in-chief of the United States Armed Forces and appoints its leaders, the secretary of defense and the Joint Chiefs of Staff. The Department of Defense, headquartered at the Pentagon near Washington, D.C., administers five of the six service branches, which are made up of the U.S. Army, Marine Corps, Navy, Air Force, and Space Force.[298] The Coast Guard is administered by the Department of Homeland Security in peacetime and can be transferred to the Department of the Navy in wartime.[299] Total strength of the entire military is about 1.3 million active duty with an additional 400,000 in reserve.
The United States spent $997 billion on its military in 2024, which is by far the largest amount of any country, making up 37% of global military spending and accounting for 3.4% of the country's GDP.[300] The U.S. possesses 42% of the world's nuclear weapons—the second-largest stockpile after that of Russia.[301] The U.S. military is widely regarded as the most powerful and advanced in the world.[302][303]
The United States has the third-largest combined armed forces in the world, behind the Chinese People's Liberation Army and Indian Armed Forces.[304] The U.S. military operates about 800 bases and facilities abroad,[305] and maintains deployments greater than 100 active duty personnel in 25 foreign countries.[306] The United States has engaged in over 400 military interventions since its founding in 1776, with over half of these occurring between 1950 and 2019 and 25% occurring in the post-Cold War era.[307]
State defense forces (SDFs) are military units that operate under the sole authority of a state government. SDFs are authorized by state and federal law but are under the command of the state's governor.[308][309][310] By contrast, the 54 U.S. National Guard organizations[t] fall under the dual control of state or territorial governments and the federal government; their units can also become federalized entities, but SDFs cannot be federalized.[311] The National Guard personnel of a state or territory can be federalized by the president under the National Defense Act Amendments of 1933; this legislation created the Guard and provides for the integration of Army National Guard and Air National Guard units and personnel into the U.S. Army and (since 1947) the U.S. Air Force.[312] The total number of National Guard members is about 430,000, while the estimated combined strength of SDFs is less than 10,000.[313]

There are about 18,000 U.S. police agencies from local to national level in the United States.[314] Law in the United States is mainly enforced by local police departments and sheriff departments in their municipal or county jurisdictions. The state police departments have authority in their respective state, and federal agencies such as the Federal Bureau of Investigation (FBI) and the U.S. Marshals Service have national jurisdiction and specialized duties, such as protecting civil rights, national security, enforcing U.S. federal courts' rulings and federal laws, and interstate criminal activity.[315] State courts conduct almost all civil and criminal trials,[316] while federal courts adjudicate the much smaller number of civil and criminal cases that relate to federal law.[317]
There is no unified "criminal justice system" in the United States. The American prison system is largely heterogenous, with thousands of relatively independent systems operating across federal, state, local, and tribal levels. In 2025, "these systems hold nearly 2 million people in 1,566 state prisons, 98 federal prisons, 3,116 local jails, 1,277 juvenile correctional facilities, 133 immigration detention facilities, and 80 Indian country jails, as well as in military prisons, civil commitment centers, state psychiatric hospitals, and prisons in the U.S. territories."[318]
Despite disparate systems of confinement, four main institutions dominate: federal prisons, state prisons, local jails, and juvenile correctional facilities.[319] Federal prisons are run by the Federal Bureau of Prisons and hold pretrial detainees as well as people who have been convicted of federal crimes.[319] State prisons, run by the department of corrections of each state, hold people sentenced and serving prison time (usually longer than one year) for felony offenses.[319] Local jails are county or municipal facilities that incarcerate defendants prior to trial; they also hold those serving short sentences (typically under a year).[319] Juvenile correctional facilities are operated by local or state governments and serve as longer-term placements for any minor adjudicated as delinquent and ordered by a judge to be confined.[320]
In January 2023, the United States had the sixth-highest per capita incarceration rate in the world—531 people per 100,000 inhabitants—and the largest prison and jail population in the world, with more than 1.9 million people incarcerated.[318][321][322] An analysis of the World Health Organization Mortality Database from 2010 showed U.S. homicide rates "were 7 times higher than in other high-income countries, driven by a gun homicide rate that was 25 times higher".[323]

The U.S. has a highly developed mixed economy[324] that has been the world's largest nominally since about 1890.[325] Its 2024 gross domestic product (GDP)[e] of more than $29 trillion[326] constituted over 25% of nominal global economic output, or 15% at purchasing power parity (PPP). From 1983 to 2008, U.S. real compounded annual GDP growth was 3.3%, compared to a 2.3% weighted average for the rest of the G7.[327] The country ranks first in the world by nominal GDP,[328] second when adjusted for purchasing power parities (PPP),[15] and ninth by PPP-adjusted GDP per capita.[15] In February 2024, the total U.S. federal government debt was $34.4 trillion.[329]

Of the world's 500 largest companies by revenue, 138 were headquartered in the U.S. in 2025,[330] the highest number of any country.[331] The U.S. dollar is the currency most used in international transactions and the world's foremost reserve currency, backed by the country's dominant economy, its military, the petrodollar system, its large U.S. treasuries market, and its linked eurodollar.[332] Several countries use it as their official currency, and in others it is the de facto currency.[333][334] The U.S. has free trade agreements with several countries, including the USMCA.[335] Although the United States has reached a post-industrial level of economic development[336] and is often described as having a service economy,[336][337] it remains a major industrial power;[338] in 2024, the U.S. manufacturing sector was the world's second-largest by value output after China's.[339]

New York City is the world's principal financial center,[341][342] and its metropolitan area is the world's largest metropolitan economy.[343] The New York Stock Exchange and Nasdaq, both located in New York City, are the world's two largest stock exchanges by market capitalization and trade volume.[344][345] The United States is at the forefront of technological advancement and innovation in many economic fields, especially in artificial intelligence; electronics and computers; pharmaceuticals; and medical, aerospace and military equipment.[346] The country's economy is fueled by abundant natural resources, a well-developed infrastructure, and high productivity.[347] The largest trading partners of the United States are the European Union, Mexico, Canada, China, Japan, South Korea, the United Kingdom, Vietnam, India, and Taiwan.[348] The United States is the world's largest importer and second-largest exporter.[u] It is by far the world's largest exporter of services.[351]
Americans have the highest average household[352] and employee income among OECD member states, and the fourth-highest median household income in 2023,[353] up from sixth-highest in 2013.[354] With personal consumption expenditures of over $18.5 trillion in 2023,[355] the U.S. has a heavily consumer-driven economy and is the world's largest consumer market.[356] The U.S. ranked first in the number of dollar billionaires and millionaires in 2023, with 735 billionaires and nearly 22 million millionaires.[357]
Wealth in the United States is highly concentrated; in 2011, the richest 10% of the adult population owned 72% of the country's household wealth, while the bottom 50% owned just 2%.[358] U.S. wealth inequality increased substantially since the late 1980s,[359] and income inequality in the U.S. reached a record high in 2019.[360] In 2024, the country had some of the highest wealth and income inequality levels among OECD countries.[361] Since the 1970s, there has been a decoupling of U.S. wage gains from worker productivity.[362] In 2016, the top fifth of earners took home more than half of all income,[363] giving the U.S. one of the widest income distributions among OECD countries.[364][362] There were about 771,480 homeless persons in the U.S. in 2024.[365] In 2022, 6.4 million children experienced food insecurity.[366] Feeding America estimates that around one in five, or approximately 13 million, children experience hunger in the U.S. and do not know where or when they will get their next meal.[367] Also in 2022, about 37.9 million people, or 11.5% of the U.S. population, were living in poverty.[368]
The United States has a smaller welfare state and redistributes less income through government action than most other high-income countries.[369][370] It is the only advanced economy that does not guarantee its workers paid vacation nationally[371] and one of a few countries in the world without federal paid family leave as a legal right.[372] The United States has a higher percentage of low-income workers than almost any other developed country, largely because of a weak collective bargaining system and lack of government support for at-risk workers.[373]

The United States has been a leader in technological innovation since the late 19th century and scientific research since the mid-20th century.[376] Methods for producing interchangeable parts and the establishment of a machine tool industry enabled the large-scale manufacturing of U.S. consumer products in the late 19th century.[377] By the early 20th century, factory electrification, the introduction of the assembly line, and other labor-saving techniques created the system of mass production.[378]
In the 21st century, the United States continues to be one of the world's foremost scientific powers,[379] though China has emerged as a major competitor in many fields.[380] The U.S. has the highest research and development expenditures of any country[381] and ranks ninth as a percentage of GDP.[382] In 2022, the United States was (after China) the country with the second-highest number of published scientific papers.[383] In 2021, the U.S. ranked second (also after China) by the number of patent applications, and third by trademark and industrial design applications (after China and Germany), according to World Intellectual Property Indicators.[384] In 2025[385][386] the United States ranked third (after Switzerland and Sweden) in the Global Innovation Index. The United States is considered to be a world leader in the development of artificial intelligence technology.[387] In 2023, the United States was ranked the second most technologically advanced country in the world (after South Korea) by Global Finance magazine.[388]

The United States has maintained a space program since the late 1950s, beginning with the establishment of the National Aeronautics and Space Administration (NASA) in 1958.[389][390] NASA's Apollo program (1961–1972) achieved the first crewed Moon landing with the 1969 Apollo 11 mission; it remains one of the agency's most significant milestones.[391][392] Other major endeavors by NASA include the Space Shuttle program (1981–2011),[393] the Voyager program (1972–present), the Hubble and James Webb space telescopes (launched in 1990 and 2021, respectively),[394][395] and the multi-mission Mars Exploration Program (Spirit, Opportunity, Curiosity, and Perseverance).[396] NASA is one of five agencies collaborating on the International Space Station (ISS);[397] U.S. contributions to the ISS include several modules, including Destiny (2001), Harmony (2007), and Tranquility (2010), as well as ongoing logistical and operational support.[398]
The United States private sector dominates the global commercial spaceflight industry.[399] Prominent American spaceflight contractors include Blue Origin, Boeing, Lockheed Martin, Northrop Grumman, and SpaceX. NASA programs such as the Commercial Crew Program, Commercial Resupply Services, Commercial Lunar Payload Services, and NextSTEP have facilitated growing private-sector involvement in American spaceflight.[400]
In 2023, the United States received approximately 84% of its energy from fossil fuel, and its largest source of energy was petroleum (38%), followed by natural gas (36%), renewable sources (9%), coal (9%), and nuclear power (9%).[401][402] In 2022, the United States constituted about 4% of the world's population, but consumed around 16% of the world's energy.[403] The U.S. ranks as the second-highest emitter of greenhouse gases behind China.[404]
The U.S. is the world's largest producer of nuclear power, generating around 30% of the world's nuclear electricity.[405] It also has the highest number of nuclear power reactors of any country.[406] From 2024, the U.S. plans to triple its nuclear power capacity by 2050.[407]

The United States' 4 million miles (6.4 million kilometers) of road network, owned almost entirely by state and local governments, is the longest in the world.[408][409] The extensive Interstate Highway System that connects all major U.S. cities is funded mostly by the federal government but maintained by state departments of transportation. The system is further extended by state highways and some private toll roads.
The U.S. is among the top ten countries with the highest vehicle ownership per capita (850 vehicles per 1,000 people) in 2022. A 2022 study found that 76% of U.S. commuters drive alone and 14% ride a bicycle, including bike owners and users of bike-sharing networks. About 11% use some form of public transportation.[410][411]
Public transportation in the United States is well developed in the largest urban areas, notably New York City, Washington, D.C., Boston, Philadelphia, Chicago, and San Francisco; otherwise, coverage is generally less extensive than in most other developed countries. The U.S. also has many relatively car-dependent localities.[412]
Long-distance intercity travel is provided primarily by airlines, but travel by rail is more common along the Northeast Corridor, the only high-speed rail in the U.S. that meets international standards. Amtrak, the country's government-sponsored national passenger rail company, has a relatively sparse network compared to that of Western European countries. Service is concentrated in the Northeast, California, the Midwest, the Pacific Northwest, and Virginia/Southeast.

The United States has an extensive air transportation network. U.S. civilian airlines are all privately owned. The three largest airlines in the world, by total number of passengers carried, are U.S.-based; American Airlines became the global leader after its 2013 merger with US Airways.[415] Of the 50 busiest airports in the world, 16 are in the United States, as well as five of the top 10.[416] The world's busiest airport by passenger volume is Hartsfield–Jackson Atlanta International in Atlanta, Georgia.[413][416] In 2022, most of the 19,969 U.S. airports[417] were owned and operated by local government authorities, and there are also some private airports. Some 5,193 are designated as "public use", including for general aviation. The Transportation Security Administration (TSA) has provided security at most major airports since 2001.
The country's rail transport network, the longest in the world at 182,412.3 mi (293,564.2 km),[418] handles mostly freight[419][420] (in contrast to more passenger-centered rail in Europe[421]). Because they are often privately owned operations, U.S. railroads lag behind those of the rest of the world in terms of electrification.[422]
The country's inland waterways are the world's fifth-longest, totaling 25,482 mi (41,009 km).[423] They are used extensively for freight, recreation, and a small amount of passenger traffic. Of the world's 50 busiest container ports, four are located in the United States, with the busiest in the country being the Port of Los Angeles.[424]
| State | Population (millions) |
|---|---|
| California | |
| Texas | |
| Florida | |
| New York | |
| Pennsylvania | |
| Illinois | |
| Ohio | |
| Georgia | |
| North Carolina | |
| Michigan |
The U.S. Census Bureau reported 331,449,281 residents on April 1, 2020,[v][426] making the United States the third-most-populous country in the world, after India and China.[427] The Census Bureau's official 2025 population estimate was 341,784,857, an increase of 3.1% since the 2020 census.[13] According to the Bureau's U.S. Population Clock, on July 1, 2024, the U.S. population had a net gain of one person every 16 seconds, or about 5400 people per day.[428] In 2023, 51% of Americans age 15 and over were married, 6% were widowed, 10% were divorced, and 34% had never been married.[429] In 2023, the total fertility rate for the U.S. stood at 1.6 children per woman,[430] and, at 23%, it had the world's highest rate of children living in single-parent households in 2019.[431] Most Americans live in the suburbs of major metropolitan areas.
The United States has a diverse population; 37 ancestry groups have more than one million members.[432] White Americans with ancestry from Europe, the Middle East, or North Africa form the largest racial and ethnic group at 57.8% of the United States population.[433][434] Hispanic and Latino Americans form the second-largest group and are 18.7% of the United States population. African Americans constitute the country's third-largest ancestry group and are 12.1% of the total U.S. population.[432] Asian Americans are the country's fourth-largest group, composing 5.9% of the United States population. The country's 3.7 million Native Americans account for about 1%,[432] and some 574 native tribes are recognized by the federal government.[435] In 2024, the median age of the United States population was 39.1 years.[436]

While many languages and dialects are spoken in the United States, English is by far the most commonly spoken and written.[437] De facto, English is the official language of the United States, and in 2025, Executive Order 14224 declared English official.[4] However, the U.S. has never had a statutory official language, as Congress has never passed a law to designate English as official for all three federal branches. Some laws, such as U.S. naturalization requirements, nonetheless standardize English. Twenty-eight states and the United States Virgin Islands have laws that designate English as the sole official language; 19 states and the District of Columbia have no official language.[438] Three states and four U.S. territories have recognized local or indigenous languages in addition to English: Hawaii (Hawaiian),[439] Alaska (twenty Native languages),[w][440] South Dakota (Sioux),[441] American Samoa (Samoan), Puerto Rico (Spanish), Guam (Chamorro), and the Northern Mariana Islands (Carolinian and Chamorro). In total, 169 Native American languages are spoken in the United States.[442] In Puerto Rico, Spanish is more widely spoken than English.[443]
According to the American Community Survey (2020),[444] some 245.4 million people in the U.S. age five and older spoke only English at home. About 41.2 million spoke Spanish at home, making it the second most commonly used language. Other languages spoken at home by one million people or more include Chinese (3.40 million), Tagalog (1.71 million), Vietnamese (1.52 million), Arabic (1.39 million), French (1.18 million), Korean (1.07 million), and Russian (1.04 million). German, spoken by 1 million people at home in 2010, fell to 881,000 estimated total speakers in 2020.[445]

America's immigrant population is by far the world's largest in absolute terms.[446][447] In 2022, there were 87.7 million immigrants and U.S.-born children of immigrants in the United States, accounting for nearly 27% of the overall U.S. population.[448] In 2017, out of the U.S. foreign-born population, some 45% (20.7 million) were naturalized citizens, 27% (12.3 million) were lawful permanent residents, 6% (2.2 million) were temporary lawful residents, and 23% (10.5 million) were unauthorized immigrants.[449] In 2019, the top countries of origin for immigrants were Mexico (24% of immigrants), India (6%), China (5%), the Philippines (4.5%), and El Salvador (3%).[450] In fiscal year 2022, over one million immigrants (most of whom entered through family reunification) were granted legal residence.[451] The undocumented immigrant population in the U.S. reached a record high of 14 million in 2023.[452]
The First Amendment guarantees the free exercise of religion in the country and forbids Congress from passing laws respecting its establishment.[453][454] Religious practice is widespread, among the most diverse in the world,[455] and profoundly vibrant.[456]
The country has the world's largest Christian population, which includes the fourth-largest population of Catholics.[457] Other notable faiths include Judaism, Buddhism, Hinduism, Islam, New Age, and Native American religions.[458] Religious practice varies significantly by region.[459] "Ceremonial deism" is common in American culture.[460]
The overwhelming majority of Americans believe in a higher power or spiritual force, engage in spiritual practices such as prayer, and consider themselves religious or spiritual.[461][462] In the Southern United States' "Bible Belt", evangelical Protestantism plays a significant role culturally; New England and the Western United States tend to be more secular.[459][463] Mormonism, a Restorationist movement founded in the U.S. in 1847,[464] is the predominant religion in Utah and a major religion in Idaho.
About 82% of Americans live in metropolitan areas, particularly in suburbs;[346] about half of those reside in cities with populations over 50,000.[465] In 2022, 333 incorporated municipalities had populations over 100,000, nine cities had more than one million residents, and four cities—New York City, Los Angeles, Chicago, and Houston—had populations exceeding two million.[466] Many U.S. metropolitan populations are growing rapidly, particularly in the South and West.[467]
|
Largest metropolitan areas in the United States
|
|||||||||
|---|---|---|---|---|---|---|---|---|---|
| Rank | Name | Region | Pop. | Rank | Name | Region | Pop. | ||
| 1 | New York | Northeast | 20,112,448 | 11 | Boston | Northeast | 5,034,221 | ||
| 2 | Los Angeles | West | 12,844,441 | 12 | Riverside–San Bernardino | West | 4,769,007 | ||
| 3 | Chicago | Midwest | 9,434,123 | 13 | San Francisco | West | 4,630,041 | ||
| 4 | Dallas–Fort Worth | South | 8,477,157 | 14 | Detroit | Midwest | 4,390,913 | ||
| 5 | Houston | South | 7,904,627 | 15 | Seattle | West | 4,161,883 | ||
| 6 | Atlanta | South | 6,482,182 | 16 | Minneapolis–Saint Paul | Midwest | 3,790,295 | ||
| 7 | Washington, D.C. | South | 6,465,724 | 17 | Tampa–St. Petersburg | South | 3,418,895 | ||
| 8 | Miami | South | 6,391,072 | 18 | San Diego | West | 3,282,248 | ||
| 9 | Philadelphia | Northeast | 6,329,118 | 19 | Denver | West | 3,092,037 | ||
| 10 | Phoenix | West | 5,228,938 | 20 | Orlando | South | 2,957,672 | ||

According to the Centers for Disease Control and Prevention (CDC), average U.S. life expectancy at birth reached 79.0 years in 2024, its highest recorded level. This was an increase of 0.6 years over 2023. The CDC attributed the improvement to a significant fall in the number of fatal drug overdoses in the country, noting that "heart disease continues to be the leading cause of death in the United States, followed by cancer and unintentional injuries."[472] In 2024, life expectancy at birth for American men rose to 76.5 years (+0.7 years compared to 2023), while life expectancy for women was 81.4 years (+0.3 years).[473] Starting in 1998, life expectancy in the U.S. fell behind that of other wealthy industrialized countries, and Americans' "health disadvantage" gap has been increasing ever since.[474]
The Commonwealth Fund reported in 2020 that the U.S. had the highest suicide rate among high-income countries.[475] Approximately one-third of the U.S. adult population is obese and another third is overweight.[476] The U.S. healthcare system far outspends that of any other country, measured both in per capita spending and as a percentage of GDP, but attains worse healthcare outcomes when compared to peer countries for reasons that are debated.[477] The United States is the only developed country without a system of universal healthcare, and a significant proportion of the population that does not carry health insurance.[478] Government-funded healthcare coverage for the poor (Medicaid) and for those age 65 and older (Medicare) is available to Americans who meet the programs' income or age qualifications. In 2010, then-President Obama passed the Patient Protection and Affordable Care Act.[x][479] Abortion in the United States is not federally protected, and is illegal or restricted in 17 states.[480]

American primary and secondary education, known in the U.S. as K–12 ("kindergarten through 12th grade"), is decentralized. School systems are operated by state, territorial, and sometimes municipal governments and regulated by the U.S. Department of Education. In general, children are required to attend school or an approved homeschool from the age of five or six (kindergarten or first grade) until they are 18 years old. This often brings students through the 12th grade, the final year of a U.S. high school, but some states and territories allow them to leave school earlier, at age 16 or 17.[482] The U.S. spends more on education per student than any other country,[483] an average of $18,614 per year per public elementary and secondary school student in 2020–2021.[484] Among Americans age 25 and older, 92.2% graduated from high school, 62.7% attended some college, 37.7% earned a bachelor's degree, and 14.2% earned a graduate degree.[485] The U.S. literacy rate is near-universal.[346][486] The U.S. has produced the most Nobel Prize winners of any country, with 411 (having won 413 awards).[487][488]
U.S. tertiary or higher education has earned a global reputation. Many of the world's top universities, as listed by various ranking organizations, are in the United States, including 19 of the top 25.[489][490] American higher education is dominated by state university systems, although the country's many private universities and colleges enroll about 20% of all American students. Local community colleges generally offer open admissions, lower tuition, and coursework leading to a two-year associate degree or a non-degree certificate.[491]
As for public expenditures on higher education, the U.S. spends more per student than the OECD average, and Americans spend more than all nations in combined public and private spending.[492] Colleges and universities directly funded by the federal government do not charge tuition and are limited to military personnel and government employees, including: the U.S. service academies, the Naval Postgraduate School, and military staff colleges. Despite some student loan forgiveness programs in place,[493] student loan debt increased by 102% between 2010 and 2020,[494] and exceeded $1.7 trillion in 2022.[495]

The United States is home to a wide variety of ethnic groups, traditions, and customs.[497][498] The country has been described as having the values of individualism and personal autonomy,[499][500] as well as a strong work ethic[501] and competitiveness.[502] Voluntary altruism towards others also plays a major role;[503][504][505] according to a 2016 study by the Charities Aid Foundation, Americans donated 1.44% of total GDP to charity—the highest rate in the world by a large margin.[506] Americans have traditionally been characterized by a unifying political belief in an "American Creed" emphasizing consent of the governed, liberty, equality under the law, democracy, social equality, property rights, and a preference for limited government.[507][508] The U.S. has acquired significant hard and soft power through its diplomatic influence, economic power, military alliances, and cultural exports such as American movies, music, video games, sports, and food.[509][510] The influence that the United States exerts on other countries through soft power is referred to as Americanization.[511]
Nearly all present Americans or their ancestors came from Europe, Africa, or Asia (the "Old World") within the past five centuries.[512] Mainstream American culture is a Western culture largely derived from the traditions of European immigrants with influences from many other sources, such as traditions brought by slaves from Africa.[513] More recent immigration from Asia and especially Latin America has added to a cultural mix that has been described as a homogenizing melting pot, and a heterogeneous salad bowl, with immigrants contributing to, and often assimilating into, mainstream American culture.
Under the First Amendment to the Constitution, the United States is considered to have the strongest protections of free speech of any country.[514] Flag desecration, hate speech, blasphemy, and lese majesty are all forms of protected expression.[515][516][517] A 2016 Pew Research Center poll found that Americans were the most supportive of free expression of any polity measured.[518] Additionally, they are the "most supportive of freedom of the press and the right to use the Internet without government censorship".[519] The U.S. is a socially progressive country[520] with permissive attitudes surrounding human sexuality.[521] LGBTQ rights in the United States are among the most advanced by global standards.[521][522][523]
The American Dream, or the perception that Americans enjoy high levels of social mobility, plays a key role in attracting immigrants.[524][525] Whether this perception is accurate has been a topic of debate.[526][527][528] While mainstream culture holds that the United States is a classless society,[529] scholars identify significant differences between the country's social classes, affecting socialization, language, and values.[530][531] Americans tend to greatly value socioeconomic achievement, but being ordinary or average is promoted by some as a noble condition as well.[532]
The National Foundation on the Arts and the Humanities is an agency of the United States federal government that was established in 1965 with the purpose to "develop and promote a broadly conceived national policy of support for the humanities and the arts in the United States, and for institutions which preserve the cultural heritage of the United States."[533] It is composed of four sub-agencies:

Colonial American authors were influenced by John Locke and other Enlightenment philosophers.[535][536] The American Revolutionary Period (1765–1783) is notable for the political writings of Benjamin Franklin, Alexander Hamilton, Thomas Paine, and Thomas Jefferson. Shortly before and after the Revolutionary War, the newspaper rose to prominence, filling a demand for anti-British national literature.[537][538] An early novel is William Hill Brown's The Power of Sympathy, published in 1791. Writer and critic John Neal in the early- to mid-19th century helped advance America toward a unique literature and culture by criticizing predecessors such as Washington Irving for imitating their British counterparts, and by influencing writers such as Edgar Allan Poe,[539] who took American poetry and short fiction in new directions. Ralph Waldo Emerson and Margaret Fuller pioneered the influential Transcendentalism movement;[540][541] Henry David Thoreau, author of Walden, was influenced by this movement.
The conflict surrounding abolitionism inspired writers, like Harriet Beecher Stowe, and authors of slave narratives, such as Frederick Douglass. Nathaniel Hawthorne's The Scarlet Letter (1850) explored the dark side of American history, as did Herman Melville's Moby-Dick (1851). Major American poets of the 19th century American Renaissance include Walt Whitman, Melville, and Emily Dickinson.[542][543] Mark Twain was the first major American writer to be born in the West. Henry James achieved international recognition with novels like The Portrait of a Lady (1881). As literacy rates rose, periodicals published more stories centered around industrial workers, women, and the rural poor.[544][545] Naturalism, regionalism, and realism were the major literary movements of the period.[546][547]
While modernism generally took on an international character, modernist authors working within the United States more often rooted their work in specific regions, peoples, and cultures.[548] Following the Great Migration to northern cities, African-American and black West Indian authors of the Harlem Renaissance developed an independent tradition of literature that rebuked a history of inequality and celebrated black culture. An important cultural export during the Jazz Age, these writings were a key influence on Négritude, a philosophy emerging in the 1930s among francophone writers of the African diaspora.[549][550] In the 1950s, an ideal of homogeneity led many authors to attempt to write the Great American Novel,[551] while the Beat Generation rejected this conformity, using styles that elevated the impact of the spoken word over mechanics to describe drug use, sexuality, and the failings of society.[552][553] Contemporary literature is more pluralistic than in previous eras, with the closest thing to a unifying feature being a trend toward self-conscious experiments with language.[554] Twelve American laureates have won the Nobel Prize in Literature.[555]

Media in the United States is broadly uncensored, with the First Amendment providing significant protections, as reiterated in New York Times Co. v. United States.[514] The four major broadcasters in the U.S. are the National Broadcasting Company (NBC), Columbia Broadcasting System (CBS), American Broadcasting Company (ABC), and Fox Broadcasting Company (Fox). The four major broadcast television networks are all commercial entities. The Public Broadcasting Service (PBS) is the country's major non-commercial public broadcast network;[556] it also provides educational programming through local PBS stations.[557][558][559][560] The U.S. cable television system offers hundreds of channels catering to a variety of niches.[561] In 2021, about 83% of Americans over age 12 listened to broadcast radio, while about 40% listened to podcasts.[562] In the prior year, there were 15,460 licensed full-power radio stations in the U.S. according to the Federal Communications Commission (FCC).[563] Public radio broadcasting is largely supplied by National Public Radio (NPR), incorporated in February 1970 under the Public Broadcasting Act of 1967.[564]
U.S. newspapers with a global reach and reputation include The Wall Street Journal, The New York Times, The Washington Post, and USA Today.[565] About 800 publications are produced in Spanish.[566][567] With few exceptions, newspapers are privately owned, either by large chains such as Gannett or McClatchy, which own dozens or even hundreds of newspapers; by small chains that own a handful of papers; or, in an increasingly rare situation, by individuals or families. Major cities often have alternative newspapers to complement the mainstream daily papers, such as The Village Voice in New York City and LA Weekly in Los Angeles. The five most-visited websites in the world are Google, YouTube, Facebook, Instagram, and ChatGPT—all of them American-owned. Other popular platforms used include X (formerly Twitter) and Amazon.[568][569]
In 2025, the U.S. was the world's second-largest video game market by revenue (after China).[570] In 2015, the U.S. video game industry consisted of 2,457 companies that employed around 220,000 jobs and generated $30.4 billion in revenue.[571] There are 444 game publishers, developers, and hardware companies in California alone.[572] According to the Game Developers Conference (GDC), the U.S. is the top location for video game development, with 58% of the world's game developers based there in 2025.[573]

The United States is well known for its theater. Mainstream theater in the United States derives from the old European theatrical tradition and has been heavily influenced by the British theater.[574] By the middle of the 19th century, America had created new distinct dramatic forms in the Tom Shows, the showboat theater and the minstrel show.[575] The central hub of the American theater scene is the Theater District in Manhattan, with its divisions of Broadway, off-Broadway, and off-off-Broadway.[576]
Many movie and television celebrities have gotten their big break working in New York productions. Outside New York City, many cities have professional regional or resident theater companies that produce their own seasons. The biggest-budget theatrical productions are musicals. U.S. theater has an active community theater culture.[577]
The Tony Awards recognizes excellence in live Broadway theater and are presented at an annual ceremony in Manhattan. The awards are given for Broadway productions and performances. One is also given for regional theater. Several discretionary non-competitive awards are given as well, including a Special Tony Award, the Tony Honors for Excellence in Theatre, and the Isabelle Stevenson Award.[578]
Folk art in colonial America grew out of artisanal craftsmanship in communities that allowed commonly trained people to individually express themselves. It was distinct from Europe's tradition of high art, which was less accessible and generally less relevant to early American settlers.[580] Cultural movements in art and craftsmanship in colonial America generally lagged behind those of Western Europe. For example, the prevailing medieval style of woodworking and primitive sculpture became integral to early American folk art, despite the emergence of Renaissance styles in England in the late 16th and early 17th centuries. The new English styles would have been early enough to make a considerable impact on American folk art, but American styles and forms had already been firmly adopted. Not only did styles change slowly in early America, but there was a tendency for rural artisans there to continue their traditional forms longer than their urban counterparts did—and far longer than those in Western Europe.[514]
The Hudson River School was a mid-19th-century movement in the visual arts tradition of European naturalism. The 1913 Armory Show in New York City, an exhibition of European modernist art, shocked the public and transformed the U.S. art scene.[581]
American Realism and American Regionalism sought to reflect and give America new ways of looking at itself. Georgia O'Keeffe, Marsden Hartley, and others experimented with new and individualistic styles, which would become known as American modernism. Major artistic movements such as the abstract expressionism of Jackson Pollock and Willem de Kooning and the pop art of Andy Warhol and Roy Lichtenstein developed largely in the United States. Major photographers include Alfred Stieglitz, Edward Steichen, Dorothea Lange, Edward Weston, James Van Der Zee, Ansel Adams, and Gordon Parks.[582]
The tide of modernism and then postmodernism has brought global fame to American architects, including Frank Lloyd Wright, Philip Johnson, and Frank Gehry.[583] The Metropolitan Museum of Art in Manhattan is the largest art museum in the United States[584] and the fourth-largest in the world.[585]

American folk music encompasses numerous music genres, variously known as traditional music, traditional folk music, contemporary folk music, or roots music. Many traditional songs have been sung within the same family or folk group for generations, and sometimes trace back to such origins as the British Isles, mainland Europe, or Africa.[586] The rhythmic and lyrical styles of African-American music in particular have influenced American music.[587] Banjos were brought to America through the slave trade. Minstrel shows incorporating the instrument into their acts led to its increased popularity and widespread production in the 19th century.[588][589] The electric guitar, first invented in the 1930s, and mass-produced by the 1940s, had an enormous influence on popular music, in particular due to the development of rock and roll.[590] The synthesizer, turntablism, and electronic music were also largely developed in the U.S.
Elements from folk idioms such as the blues and old-time music were adopted and transformed into popular genres with global audiences. Jazz grew from blues and ragtime in the early 20th century, developing from the innovations and recordings of composers such as W.C. Handy and Jelly Roll Morton. Louis Armstrong and Duke Ellington increased its popularity early in the 20th century.[591] Country music developed in the 1920s,[592] bluegrass[593] and rhythm and blues in the 1940s,[594] and rock and roll in the 1950s.[590] In the 1960s, Bob Dylan emerged from the folk revival to become one of the country's most celebrated songwriters.[595] The musical forms of punk and hip hop both originated in the United States in the 1970s.[596]
The United States has the world's largest music market, with a total retail value of $15.9 billion in 2022.[597] Most of the world's major record companies are based in the U.S.; they are represented by the Recording Industry Association of America (RIAA).[598] Mid-20th-century American pop stars, such as Frank Sinatra[599] and Elvis Presley,[600] became global celebrities and best-selling music artists,[591] as have artists of the late 20th century, such as Michael Jackson,[601] Madonna,[602] Whitney Houston,[603] and Mariah Carey,[604] and of the early 21st century, such as Eminem,[605] Britney Spears,[606] Lady Gaga,[606] Katy Perry,[606] Taylor Swift and Beyoncé.[607]

The United States has the world's largest apparel market by revenue.[608] Apart from professional business attire, American fashion is eclectic and predominantly informal. Americans' diverse cultural roots are reflected in their clothing; however, sneakers, jeans, T-shirts, and baseball caps are emblematic of American styles.[609] New York, with its Fashion Week, is considered to be one of the "Big Four" global fashion capitals, along with Paris, Milan, and London. A study demonstrated that general proximity to Manhattan's Garment District has been synonymous with American fashion since its inception in the early 20th century.[610]
A number of well-known designer labels, among them Tommy Hilfiger, Ralph Lauren, Tom Ford and Calvin Klein, are headquartered in Manhattan.[611][612] Labels cater to niche markets, such as preteens. New York Fashion Week is one of the most influential fashion shows in the world, and is held twice each year in Manhattan;[613] the annual Met Gala, also in Manhattan, has been called the fashion world's "biggest night".[614][615]

The U.S. film industry has a worldwide influence and following. Hollywood, a district in central Los Angeles, the nation's second-most populous city, is also metonymous for the American filmmaking industry.[616][617][618] The major film studios of the United States are the primary source of the most commercially successful movies selling the most tickets in the world.[619][620]
Largely centered in the New York City region from its beginnings in the late 19th century through the first decades of the 20th century,[621][622][623][624] the U.S. film industry has since been primarily based in and around Hollywood. Nonetheless, American film companies have been subject to the forces of globalization in the 21st century, and an increasing number of films are made elsewhere.[625] The Academy Awards, popularly known as "the Oscars", have been held annually by the Academy of Motion Picture Arts and Sciences since 1929,[626] and the Golden Globe Awards have been held annually since January 1944.[627]
The industry peaked in what is commonly referred to as the "Golden Age of Hollywood", from the early sound period until the early 1960s,[628] with screen actors such as John Wayne and Marilyn Monroe becoming iconic figures.[629][630] In the 1970s, "New Hollywood", or the "Hollywood Renaissance",[631] was defined by grittier films influenced by French and Italian realist pictures of the post-war period.[632] The 21st century has been marked by the rise of American streaming platforms, which came to rival traditional cinema.[633][634]

Early settlers were introduced by Native Americans to foods such as turkey, sweet potatoes, corn, squash, and maple syrup. Of the most enduring and pervasive examples are variations of the native dish called succotash. Early settlers and later immigrants combined these with foods they were familiar with, such as wheat flour,[635] beef, and milk, to create a distinctive American cuisine.[636][637] New World crops, especially pumpkin, corn, potatoes, and turkey as the main course are part of a shared national menu on Thanksgiving, when many Americans prepare or purchase traditional dishes to celebrate the occasion.[638]
Characteristic American dishes such as apple pie, fried chicken, doughnuts, french fries, macaroni and cheese, ice cream, hamburgers, hot dogs, and American pizza derive from the recipes of various immigrant groups.[639][640][641][642] Mexican dishes such as burritos and tacos preexisted the United States in areas later annexed from Mexico, and adaptations of Chinese cuisine as well as pasta dishes freely adapted from Italian sources are all widely consumed.[643]
American chefs have had a significant impact on society both domestically and internationally. In 1946, the Culinary Institute of America was founded by Katharine Angell and Frances Roth. This would become the United States' most prestigious culinary school, where many of the most talented American chefs would study prior to successful careers.[644][645] The United States restaurant industry was projected at $899 billion in sales for 2020,[646][647] and employed more than 15 million people, representing 10% of the nation's workforce directly.[646] It is the country's second-largest private employer and the third-largest employer overall.[648][649] The United States is home to over 220 Michelin star-rated restaurants, 70 of which are in New York City.[650]
Wine has been produced in what is now the United States since the 1500s, with the first widespread production beginning in what is now New Mexico in 1628.[651][652][653] In the modern U.S., wine production is undertaken in all fifty states, with California producing 84 percent of all U.S. wine. With more than 1,100,000 acres (4,500 km2) under vine, the United States is the fourth-largest wine-producing country in the world, after Italy, Spain, and France.[654][655]
The classic American diner, a casual restaurant type originally intended for the working class, emerged during the 19th century from converted railroad dining cars made stationary. The diner soon evolved into purpose-built structures whose number expanded greatly in the 20th century.[656] The American fast-food industry developed alongside the nation's car culture.[657] American restaurants developed the drive-in format in the 1920s, which they began to replace with the drive-through format by the 1940s.[658][659] American fast-food restaurant chains, such as McDonald's, Burger King, Chick-fil-A, Kentucky Fried Chicken, Dunkin' Donuts and many others, have numerous outlets around the world.[660]

The most popular spectator sports in the U.S. are American football, basketball, baseball, soccer, and ice hockey.[661] Their premier leagues are, respectively, the National Football League, the National Basketball Association,[662] Major League Baseball,[663] Major League Soccer,[664] and the National Hockey League,[665] All these leagues enjoy wide-ranging domestic media coverage and, except for the MLS, all are considered the preeminent leagues in their respective sports in the world. While most major U.S. sports such as baseball and American football have evolved out of European practices, basketball, volleyball, skateboarding, and snowboarding are American inventions, many of which have become popular worldwide.[666] Lacrosse and surfing arose from Native American and Native Hawaiian activities that predate European contact.[667] The market for professional sports in the United States was approximately $69 billion in July 2013, roughly 50% larger than that of Europe, the Middle East, and Africa combined.[668]
American football is by several measures the most popular spectator sport in the United States.[669] Although American football does not have a substantial following in other nations, the NFL does have the highest average attendance (67,254) of any professional sports league in the world.[670] In the year 2024, the NFL generated over $23 billion, making them the most valued professional sports league in the United States and the world.[671] Baseball has been regarded as the U.S. "national sport" since the late 19th century. The most-watched individual sports in the U.S. are golf and auto racing, particularly NASCAR and IndyCar.[672][673]
On the collegiate level, earnings for the member institutions exceed $1 billion annually,[674] and college football and basketball attract large audiences, as the NCAA March Madness tournament and the College Football Playoff are some of the most watched national sporting events.[675] In the U.S., the intercollegiate sports level serves as the main feeder system for professional and Olympic sports, with significant exceptions such as Minor League Baseball. This differs greatly from practices in nearly all other countries, where publicly and privately funded sports organizations serve this function.[676]
Eight Olympic Games have taken place in the United States. The 1904 Summer Olympics in St. Louis, Missouri, were the first-ever Olympic Games held outside of Europe.[677] The Olympic Games will be held in the U.S. for a ninth time when Los Angeles hosts the 2028 Summer Olympics. U.S. athletes have won a total of 2,968 medals (1,179 gold) at the Olympic Games, the most of any country.[678][679][680]
In other international competition, the United States is the home of a number of prestigious events, including the America's Cup, World Baseball Classic, the U.S. Open, and the Masters Tournament. The U.S. men's national soccer team has qualified for eleven World Cups, while the women's national team has won the FIFA Women's World Cup and Olympic soccer tournament four and five times, respectively.[681] The 1999 FIFA Women's World Cup was hosted by the United States. Its final match was attended by 90,185, setting the world record for largest women's sporting event crowd at the time.[682] The United States hosted the 1994 FIFA World Cup and will co-host, along with Canada and Mexico, the 2026 FIFA World Cup.[683]
reflect base feature updates made in the MAF/TIGER database through August, 2010.
Archaeological evidence, in fact, recognizes that people started to leave Beringia for the New World around 40,000 years ago, but rapid expansion into North America didn't occur until about 15,000 years ago, when the ice had literally broken
By the end of the Civil War, roughly 179,000 black men (10% of the Union army) served as soldiers in the U.S. Army and another 19,000 served in the Navy.
...the so-called sexual revolution in the United States in the 1960s, marked by greatly more permissive attitudes toward sexual interest and activity than had been prevalent in earlier generations.
Now evidence is mounting that a global reversal is challenging a series of established democracies, including the United States who were downgraded by both Freedom House and V-Dem in 2018.
Prominent cross-national measures of democracy from the Varieties of Democracy Project (V-Dem), Bright Line Watch, and Freedom House, which had once ranked the country as a global leader, show a U.S. democracy slipping toward "mixed regime" or "illiberal democracy" status.
As with the Beer Hall Putsch, a would-be leader tried to take advantage of an already scheduled event (in Hitler's case, Kahr's speech; in Trump's, Congress's tallying of the electoral votes) to create a dramatic moment with himself at the center of attention, calling for bold action to upend the political order. Unlike Hitler's coup attempt, Trump already held top of office, so he was attempting to hold onto power, not seize it (the precise term for Trump's intended action is a 'self-coup' or 'autogolpe'). Thus, Trump was able to plan for the event well in advance, and with much greater control, including developing the legal arguments that could be used to justify rejecting the election's results.(p. 3)
What the United States went through on January 6th was an attempt at a self-coup, where Trump would use force to stay as head of state even if abandoning democratic practices in the U.S. Some advised Trump to declare martial law to create a state of emergency and use that as an excuse to stay in power.
[Trump] tried to delegitimize the election results by disseminating a series of far fetched and evidence-free claims of fraud. Meanwhile, with a ring of close confidants, Trump conceived and implemented unprecedented schemes to – in his own words – "overturn" the election outcome. Among the results of this "Big Lie" campaign were the terrible events of January 6, 2021 – an inflection point in what we now understand was nothing less than an attempted coup.
A good case can be made that the storming of the Capitol qualifies as a coup. It's especially so because the rioters entered at precisely the moment when the incumbent's loss was to be formally sealed, and they succeeded in stopping the count.
Because its object was to prevent a legitimate president-elect from assuming office, the attack was widely regarded as an insurrection or attempted coup d'état.
cite web: CS1 maint: bot: original URL status unknown (link)During peacetime it is part of the Department of Homeland Security. During wartime, or when the president or Congress so direct, it becomes part of the Department of Defense and is included in the Department of the Navy.
The US has a mixed economy because both private businesses and the government are important.
The New York metro area dwarfs all other cities for economic output by a large margin.
In the United States, the average household net adjusted disposable income per capita is USD 45 284 a year, much higher than the OECD average of USD 33 604 and the highest figure in the OECD.
The United States is the only advanced economy that does not federally mandate any paid vacation days or holidays.
It was this secret sauce [...] that provided the spark for the biggest and most powerful technology hub in the world.
For decades it has been the beating heart of the tech industry, the place where the future is created and where anyone who wants to be part of it has to come in search of inspiration and funding.
As predicted, in post-industrial societies, characterized by predominately liberal social cultures, like the US, Sweden, and UK...
...(the United States and [Western] Europe) as "already in crisis" for their permissive attitudes toward nonnormative sexualities...
13.) United States
In the late 1980s and early 1990s, a dramatic wave began to form in the waters of public opinion: American attitudes involving homosexuality began to change... The transformation of America's response to homosexuality has been — and continues to be — one of the most rapid and sustained shifts in mass attitudes since the start of public polling.
"Tesla, Master of Lightning", New Voyage Communications for PBS Television Network, 2000, 90 minutes.
Suarez joined the PBS NewsHour in 1999 and was a senior correspondent for the evening news program on the PBS television network until 2013.
We are pleased to announce the release of Inside Peace throughout the PBS television network in the United States.
Spanning just about 20 square blocks between Times Square and Penn Station along Seventh Avenue (also known as "Fashion Avenue"), the vibrant and always-busy neighborhood has a long and rich history that has become synonymous with American fashion since its inception more than a century ago.
When Hollywood, California, was mostly orange groves, Fort Lee, New Jersey, was a center of American film production.
Back in 1912, when Hollywood had more cattle than cameras, Fort Lee was the center of the cinematic universe. Icons from the silent era like Mary Pickford, Lionel Barrymore, and Lillian Gish crossed the Hudson River via ferry to emote on Fort Lee back lots.
Presidential environmental policies, 1933–2009
story of American freedom.
</ref>
![]() This article incorporates text from a free content work. Licensed under CC BY-SA IGO 3.0 (license statement/permission). Text taken from World Food and Agriculture – Statistical Yearbook 2023, FAO, FAO.
This article incorporates text from a free content work. Licensed under CC BY-SA IGO 3.0 (license statement/permission). Text taken from World Food and Agriculture – Statistical Yearbook 2023, FAO, FAO.